New Relic Advance: Product Keynote


Discover expert led podcasts, articles, and news from enterprise technology leaders at EM360Tech, your source for B2B tech intelligence


Here's how to rethink incident response to include detection, diagnosis, and response to third-party cloud outages.

We break down how self-healing infrastructure really works and why platform maturity now defines enterprise resilience.
This episode of Don’t Panic! It’s Just Data explores the gap between AI ambition and organisational readiness, focusing on why many AI initiatives fail to move beyond early-stage pilots.
Ostra Security Founder Michael Kennedy tells the host, Richard Stiennon why breaches are system failures, not human error and what outcome-based security metrics look like.
We examine how new AI systems are moving beyond chat and starting to perform real knowledge work inside enterprise workflows.

This episode of Tech Transformed explores how ecommerce teams can drive sustainable revenue and conversion growth in a high-cost and high-expectation market.
We break down the top data governance frameworks shaping enterprise strategy in 2026 and how to choose the right one.
Zafran CISO Nathan Rollings explains how Agentic AI & contextual exposure management are replacing CVSS to focus on the 1-in-50k vulnerabilities.
Attackers have evolved their tactics. Environments have become more complex. And the economics of alert-driven security are growing increasingly unsustainable.

This episode explores why many enterprise AI initiatives fail to deliver measurable business value, highlighting the “revenue data gap” between AI ambition and real financial impact.

This episode explores the “trust paradox” in enterprise AI, where rising executive confidence and rapid AI adoption are outpacing data quality, governance, and organisational readiness.

Policy without infrastructure is documentation. Infrastructure without policy is monitoring. Neither one produces trust on its own.
We examine why cybersecurity risk challenges traditional consumer protection and what this means for organisations responsible for digital systems.
By automating complex workflows, a new breed of artificial intelligence is moving beyond chatbots to become the autonomous engine of global business. But as companies hand over the keys, are we ready for the consequences?

Jain shares what inspired the show, how the relationship between data and AI is evolving, and why community and transparency are becoming critical to the industry’s next phase.
Root examines why dependency pinning is emerging as a core security control as software supply chain risks continue to evolve
Sam Woodcock, Sr Director at 11:11 Systems, talks about recovering from cyberattacks, based on a global survey.
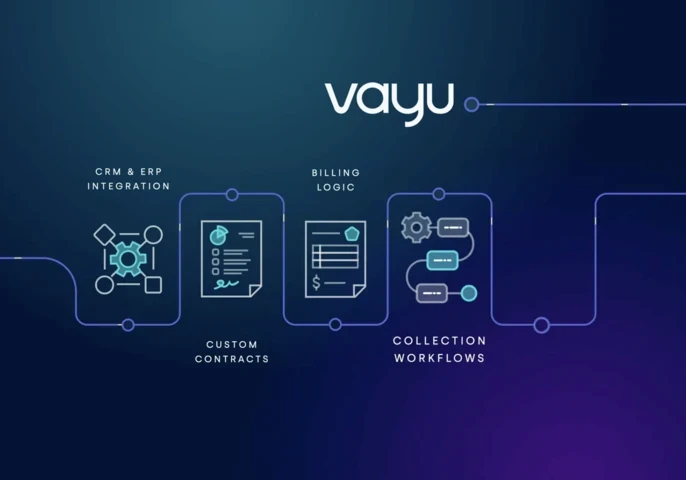

Discover how VI Labs moved from manual billing to automated revenue operations at scale using Vayu.
Get the latest insights, analysis and tech news delivered straight to your inbox