AI Agents Will Know Your “Intentions” Before You Do. It’s Called “Intention Economy”

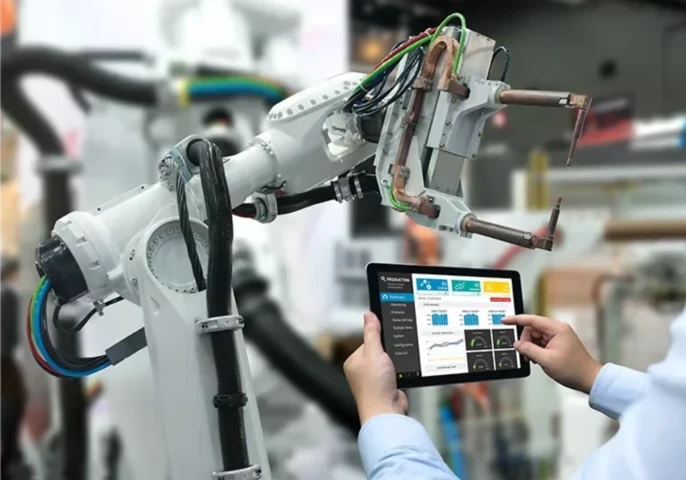
Attackers are not targeting the assets organisations know about. They are exploiting the ones nobody is tracking. Rob Gurzeev explains how AI-driven attack surface management is reshaping modern cyber defence.


Discover expert led podcasts, articles, and news from enterprise technology leaders at EM360Tech, your source for B2B tech intelligence



Large Language Models (LLM's) are reshaping how we interact with technology and consume information online.
The Head of GSMA Foundry, and lead for Connected Industries at MWC25, Richard Cockle, discusses why the industry is at a turning point as telcos look to move beyond traditional connectivity, plus why GSMA’s Connected Communities can help the journey

An executive buyer's guide
Great digital experiences demand more comprehensive monitoring
Massive investments in AI require robust monitoring of performance, risk, and results







Get the latest insights, analysis and tech news delivered straight to your inbox