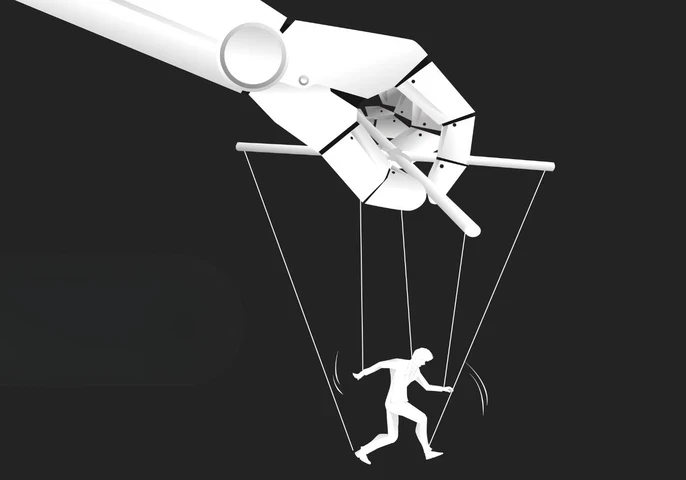
Episode 10 – AI and Observability in Workload Automation and Orchestration

Mindfuel CEO Nadiem von Heydebrand joins Christina Stathopoulos to discuss AI ROI, use case management, and how organisations can turn data initiatives into measurable business outcomes.

Discover expert led podcasts, articles, and news from enterprise technology leaders at EM360Tech, your source for B2B tech intelligence








Get the latest insights, analysis and tech news delivered straight to your inbox