Google Shopping Undergoes AI Mode Transformation

AI agents are now acting inside enterprise systems with human-level access. Richard Stiennon and Jasson Casey discuss what it actually takes to see, track, and control what they do in real time.


Discover expert led podcasts, articles, and news from enterprise technology leaders at EM360Tech, your source for B2B tech intelligence

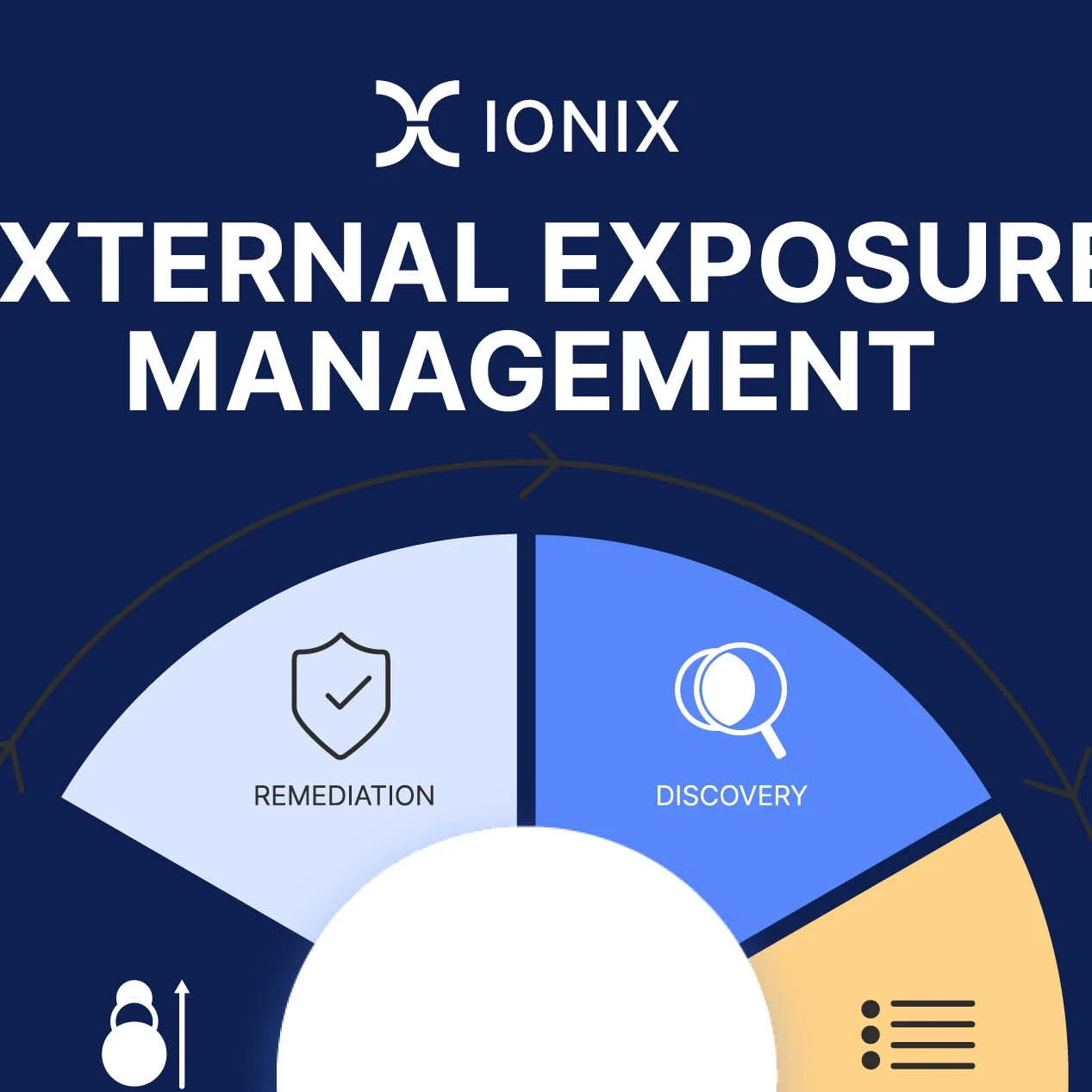
Feature Overview



“We are on the cusp of a breakthrough as we see its principles being applied to computing in ways that could transform the digital world” – Brian Cox







Get the latest insights, analysis and tech news delivered straight to your inbox