How to Leverage AIOps in Enterprise Management
Mihir Nanavati and Doug Laney explore how AI agents are transforming customer data platforms, reshaping AdTech, and changing how enterprises make marketing decisions.


Discover expert led podcasts, articles, and news from enterprise technology leaders at EM360Tech, your source for B2B tech intelligence
EM360Tech explores how client-server architecture is adapting to power today’s distributed, cloud-integrated enterprise systems.

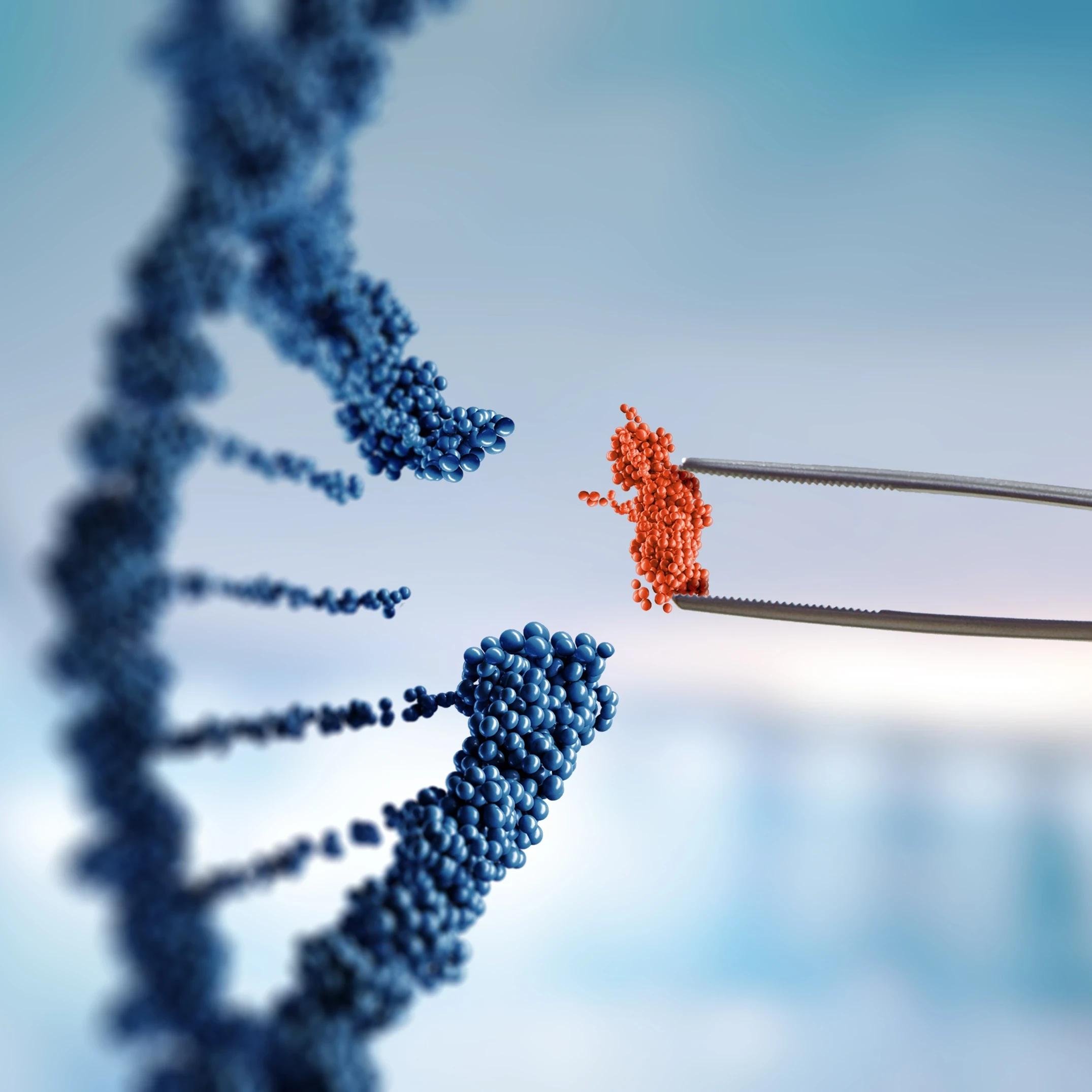
Through the adoption of advanced enterprise storage solutions, organisations can deploy their AI powered systems with confidence and avoid problems with hallucinations.
Voice search dominates 2025. Marketers must create conversational, mobile-friendly, and AI-optimized content to boost visibility, user experience, and traffic across voice-enabled devices.

For years, I've watched IT security professionals cling to outdated defensive strategies. They're building digital fortresses while the world has already moved to a completely distributed model of work and technology.

EM360Tech unpacks the role of data pipelines in scaling enterprise systems and accelerating decision-making.

Highlight how observability tools helps teams to predict, prevent, and resolve infrastructure issues before they impact users.


Get the latest insights, analysis and tech news delivered straight to your inbox