Security teams don’t have a data shortage. They have a clarity shortage.
Most enterprise environments now generate more telemetry than analysts can realistically interpret in real time. Logs stream in from identity providers, cloud platforms, endpoints, applications, networks, email gateways, and security tools that all describe risk in slightly different ways. The problem isn’t getting the data in.
It’s turning that data into decisions quickly enough to matter. That pressure is only getting worse as attack volume, identity abuse, and operational complexity keep climbing. Verizon’s 2025 DBIR analysed 22,052 real-world incidents, including 12,195 confirmed breaches, while IBM’s 2025 Cost of a Data Breach report puts the global average breach cost at USD 4.4 million.
That’s where Python becomes useful. Not as a replacement for a security information and event management (SIEM) platform, a security orchestration, automation, and response (SOAR) tool, or an extended detection and response (XDR) stack. And not as a vanity exercise in teaching analysts to code for the sake of it.
Its value is much simpler than that. Python gives security teams a flexible way to clean, reshape, correlate, enrich, and investigate data without adding yet another rigid interface to work around. It helps bridge the gap between raw telemetry and usable insight.
Why Security Teams Are Struggling With Their Own Data
The modern security stack was supposed to make teams faster. In many environments, it has done the opposite.
The volume problem is now a clarity problem
Security data has grown faster than most teams’ ability to interpret it. A single investigation might now involve identity logs from Microsoft Entra ID or Okta, endpoint telemetry from an endpoint detection and response (EDR) tool, cloud activity from Amazon Web Services (AWS) or Microsoft Azure, authentication traces, threat intelligence indicators, and a handful of email artefacts.
That sounds comprehensive until someone actually has to work through it under pressure.
The issue isn’t whether the data exists. It’s whether it arrives in a form that can be trusted, compared, and acted on. If one source uses one timestamp format, another uses a different naming convention, and a third stores key values inside nested fields, the analyst’s first job becomes translation.
That isn't high-value security work. It’s administrative friction wearing a technical disguise.
Tooling doesn’t always translate into insight
More tools don’t automatically produce more understanding. Splunk’s State of Security 2025 found that 46 per cent of teams spend more time maintaining tools than defending the organisation. That’s a brutal number, but not a surprising one. Security platforms often solve one problem well while creating another.
They centralise data, then make ad hoc analysis awkward. They promise automation, then demand constant care and feeding. They surface alerts, but not always the context needed to judge them quickly.
This is why so many teams still export data into spreadsheets, local scripts, or notebooks when the real work starts. They need room to ask better questions than the dashboard was built to answer.
Detection engineering is becoming a core capability
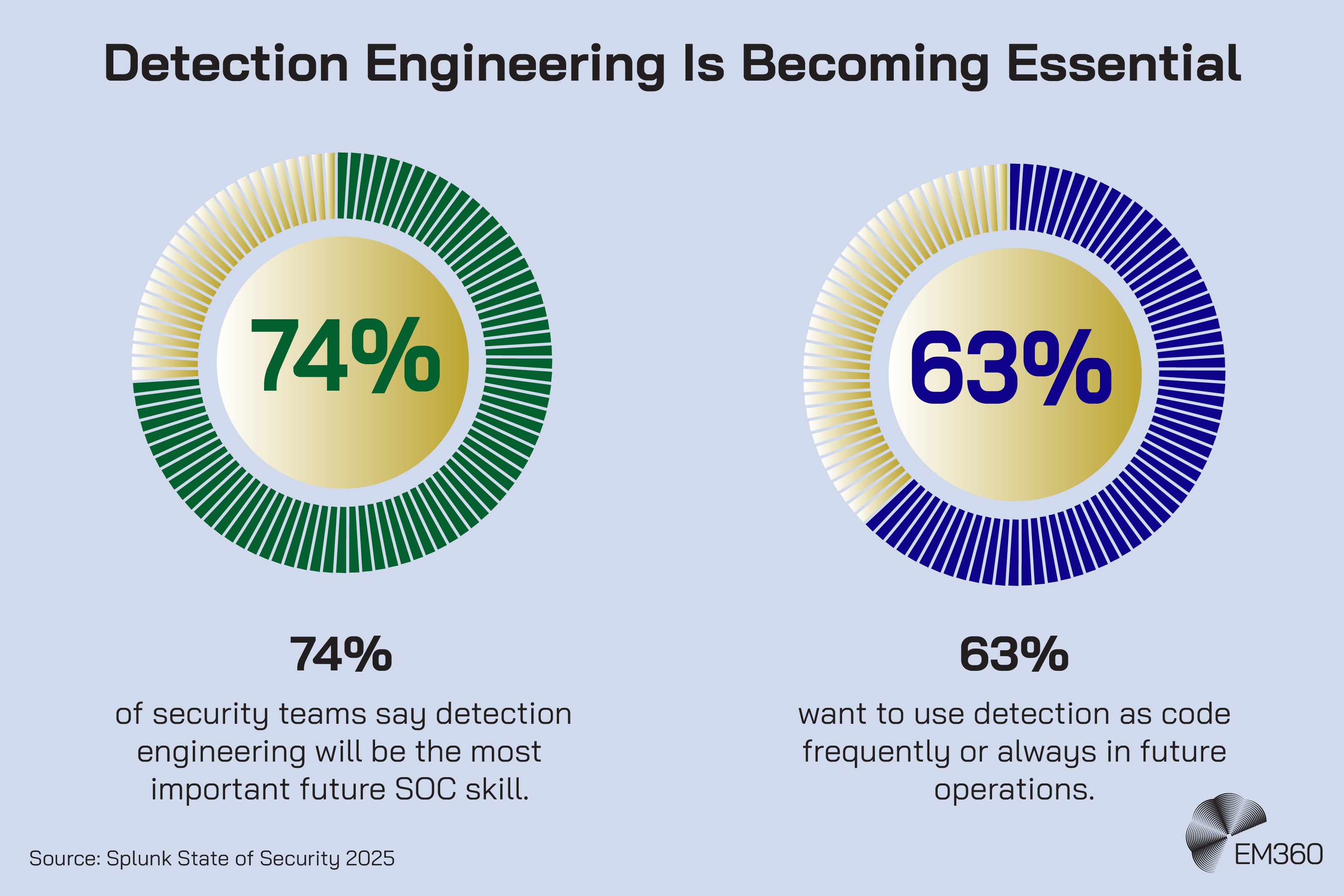
That shift is feeding a broader change in how mature teams think about detection. Detection engineering is no longer a niche discipline sitting off to one side of the security operations centre (SOC). It's becoming central to how teams improve quality, reduce noise, and make detections more testable over time.
Splunk found that 74 per cent of respondents rate detection engineering as the most important future SOC skill, while 63 per cent want to use detection as code frequently or always in future.
When AI Agents Become Users
Steve Povolny explains why security teams must govern autonomous agents as first-class identities to keep pace with AI-driven operations.
That matters here because Python fits naturally into this world. It supports testing, transformation, validation, and repeatability. In other words, it helps teams treat analysis less like a one-off scramble and more like an operational capability.
Where Python Fits In Modern Security Workflows
Python works best when it removes friction from real workflows security teams already have.
Turning raw logs into structured, usable data
One of Python’s most practical strengths is data cleaning. Security teams rarely receive perfectly shaped data. They receive flat files, API outputs, JavaScript Object Notation (JSON), comma-separated values (CSV), nested records, and fields that are technically present but operationally useless until someone normalises them.
Python makes that normalisation easier. A script can parse log formats, standardise timestamps, rename inconsistent fields, noise, and convert messy input into structured data that can actually be compared.
That matters when you need to line up authentication failures across systems, isolate unusual process chains, or make cloud activity readable enough for an analyst to work with at speed.
Enriching security data with context
Security data only becomes useful when it's placed in context. An internet protocol (IP) address on its own tells you very little. The same IP tied to known malicious infrastructure, a failed login burst, a rare geolocation, and a privileged account tells you much more.
Python is well suited to this enrichment work. It can pull in internal asset data, user information, ticketing context, vulnerability records, or external threat intelligence feeds and stitch them together around an event stream.
That kind of correlation helps teams move beyond isolated alerts and towards a clearer story about what is happening and why it matters.
Detecting anomalies across identity and behaviour
This is especially relevant now that identity has become such a dominant attack surface. Microsoft’s 2025 Digital Defense Report says more than 97 per cent of identity attacks are still password spray or brute force attacks, and identity-based attacks rose 32 per cent in the first half of 2025.
Inside the New Blockchain Stack
See how MPC custody, SIEM-integrated on-chain monitoring and off-exchange settlement are reshaping enterprise blockchain controls.

It also reports that modern multi-factor authentication can reduce identity compromise risk by more than 99 per cent.
For defenders, that means identity telemetry deserves far more attention than a static rule can usually provide. Python gives teams a way to look for unusual behaviour patterns across sign-ins, locations, device changes, access requests, token usage, and service-to-service activity.
That doesn’t mean every SOC needs to build a machine learning pipeline tomorrow. It means analysts need practical ways to spot what looks normal, what does not, and what changed.
Supporting faster incident investigation
Investigation speed still matters. Google Cloud’s M-Trends 2025 puts median global dwell time at 11 days. That's an improvement on older eras of incident response, but it's still a long time for attackers to move, persist, and escalate if defenders are slow to connect the dots.
Python helps here because it gives analysts direct control over filtering, joining, sorting, and examining data on their own terms. Instead of waiting for someone to build a new dashboard or change a search parser, they can test a hypothesis immediately. That kind of flexibility is often the difference between a promising lead and a dead end.
The Python Tools That Matter For Security Teams
Not every Python tool deserves equal attention in a security workflow. A few matter much more than the rest.
Data handling with Pandas and NumPy
Pandas and NumPy sit at the centre of most Python data work for a reason. Pandas gives teams a practical way to work with tabular data at scale, while NumPy handles fast numerical operations underneath much of the wider ecosystem.
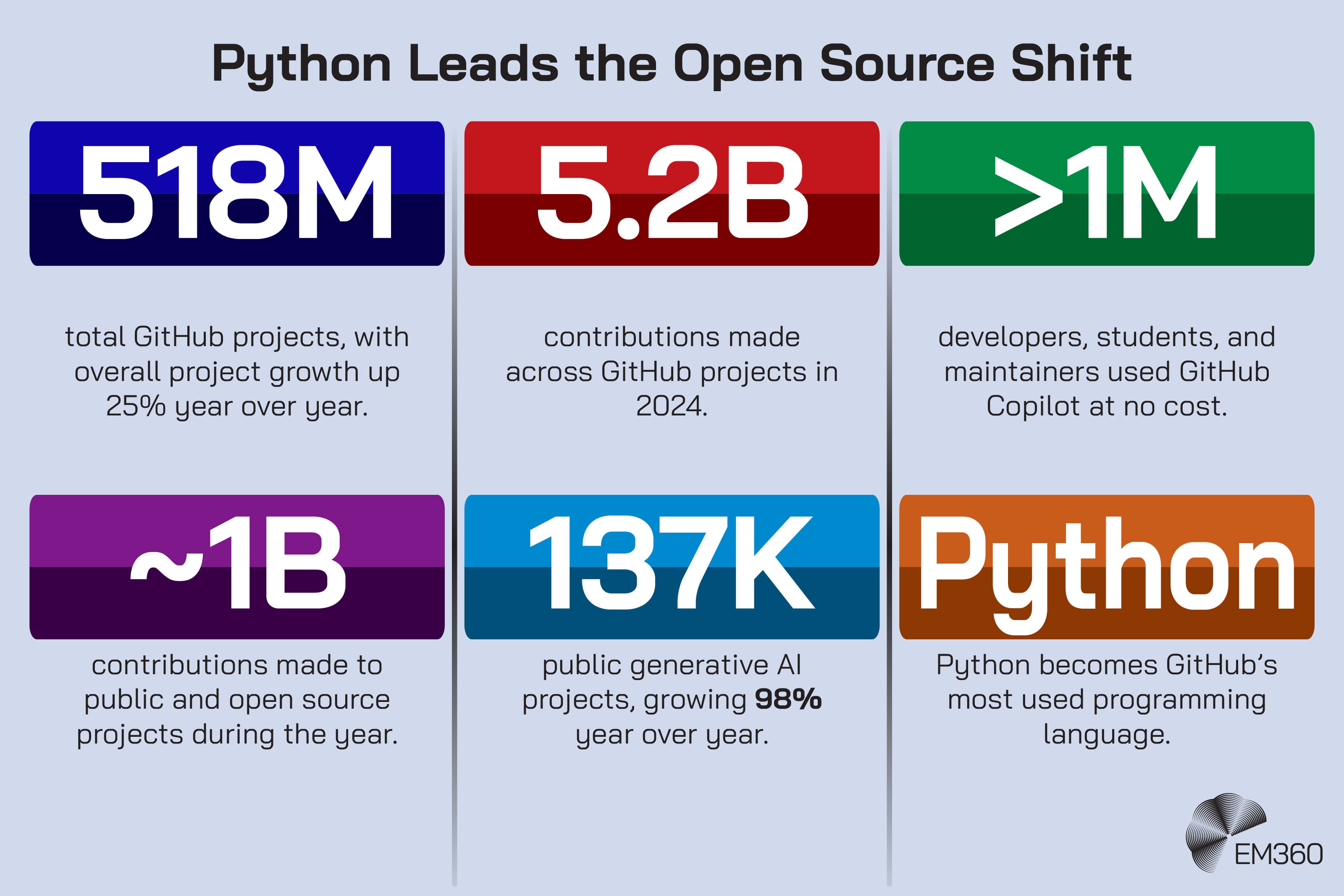
GitHub’s Octoverse 2024 reported that Python became the most used language on GitHub for the first time, which says a lot about how mainstream this ecosystem now is.

Why Cyber Attacks Are So Costly
Explores how modern attacks convert data loss and downtime into escalating fines, customer churn, and strategic security spend.
For security teams, the value is straightforward. Pandas makes it easier to group events, compare fields, filter suspicious activity, and reshape large datasets without fighting every step. The project’s official documentation also shows a stronger push towards PyArrow support for performance, richer data types, and better interoperability.
That isn't the kind of detail most CISOs need to lose sleep over, but it does point to a data stack that's still maturing in useful ways.
Visualisation and pattern recognition
Visualisation still has a place in security analysis when it's used properly. A chart can't solve an investigation for you, but it can make clusters, spikes, outliers, and behavioural patterns obvious much faster than a wall of raw rows can.
Python libraries such as Matplotlib are useful here because they let teams produce targeted visuals from the same data they are already analysing. That's often more useful than opening a separate business intelligence layer for quick pattern work, especially during an active investigation or hunt.
Machine learning for threat detection
Machine learning is where a lot of security conversations go off the rails. It's useful, but it's not magical, and most teams don't need to start with an elaborate model to get value from Python-based analysis.
What matters more is using machine learning carefully where it fits. That may mean clustering similar events, identifying outliers, helping score risk, or supporting anomaly detection in high-volume data. Used well, it can help teams prioritise. Used badly, it just produces another confident-looking stream of noise.
The goal is better judgement, not more mystique.
Working in notebooks without breaking security
Jupyter notebooks are popular because they make data work interactive and fast. That convenience is real. So is the risk. Project Jupyter’s own security guidance is explicit that the security subproject exists to reduce risk in using, deploying, operating, or developing Jupyter software.
The older Jupyter Notebook security documentation is also blunt about the fact that notebook server access effectively means the ability to run arbitrary code.
Inside Cybersecurity's New Hubs
How global cyber leaders use London’s International Cyber Expo to align strategy, strengthen resilience and shape the next wave of security standards.

That does not mean notebooks should be banned. It means they should be governed. If analysts are working with sensitive security data in notebooks, access, isolation, credential handling, and environment control matter just as much as the code itself.
The Risks Teams Need To Address Before Scaling This Approach
Python can improve security analysis. It can also introduce new exposure if teams adopt it carelessly.
Open source and supply chain risk
This is the big one. Python’s strength is its ecosystem, but open source convenience comes with supply chain risk. In April 2026, PyPI published an incident report on supply chain attacks involving the LiteLLM and Telnyx packages, along with guidance for Python developers and maintainers on how to prepare and protect themselves.
The lesson isn't that Python packages are unsafe by default. It's that teams can't treat package installation like a harmless background task. Version pinning, package review, trusted repositories, software bill of materials (SBOM) practices, and environment separation all matter more than many teams would like to admit.
Data handling and privacy exposure
A second risk is moving sensitive data into analysis environments that were never designed to handle it properly. Security teams often work with identity records, internal addresses, endpoint traces, emails, privileged account activity, and investigation notes.
That data should not be copied into unmanaged laptops, personal notebook environments, or shared workspaces just because a script runs more easily there.
The governance point here is simple. If Python becomes part of the security workflow, then the environments around it need to be treated like security infrastructure, not analyst side projects.
Skill gaps and operational readiness
There’s also a human reality to deal with. Not every analyst wants to code. Not every engineer wants to maintain data workflows. And not every organisation has the time or leadership patience to support that shift properly.
That’s why Python adoption should be tied to operational needs, not abstract “upskilling” goals. If the work becomes easier, faster, clearer, or more repeatable, people will usually see the point. If it feels like homework bolted onto an already overloaded team, they won't.
What Practical Adoption Looks Like For Enterprise Security Teams
The strongest adoption paths are usually the least glamorous ones.
Start with high-impact use cases
Begin where the friction already hurts. That might be log analysis, alert enrichment, identity monitoring, phishing investigation support, or cloud activity review. These are areas where teams already lose time cleaning data and stitching context together by hand.
If Python can remove those repetitive steps, it earns its place quickly.
Build around repeatable workflows, not one-off scripts
One of the fastest ways to create technical debt is to let useful scripts pile up without structure. The first version solves a problem. The fifth version lives on one person’s machine. The tenth version becomes folklore.
A better model is to treat successful scripts as the start of repeatable workflows. Add documentation. Standardise inputs. Control access. Test what matters. Put versioning around it. The goal isn't to turn every SOC into a software engineering team. It's to stop useful analysis from becoming fragile.
Align with detection engineering and existing platforms
Python should complement existing platforms, not compete with them. It works well when it fills the gaps around SIEM, SOAR, and XDR workflows. That might mean pre-processing messy data before ingestion, testing detection logic, enriching alerts, or validating behavioural hypotheses before formalising them into production content.
This is also where Python aligns neatly with the wider detection engineering shift. It helps teams move from static alert logic towards something more testable, adaptable, and evidence-led. Splunk’s research on detection as code points in exactly that direction.
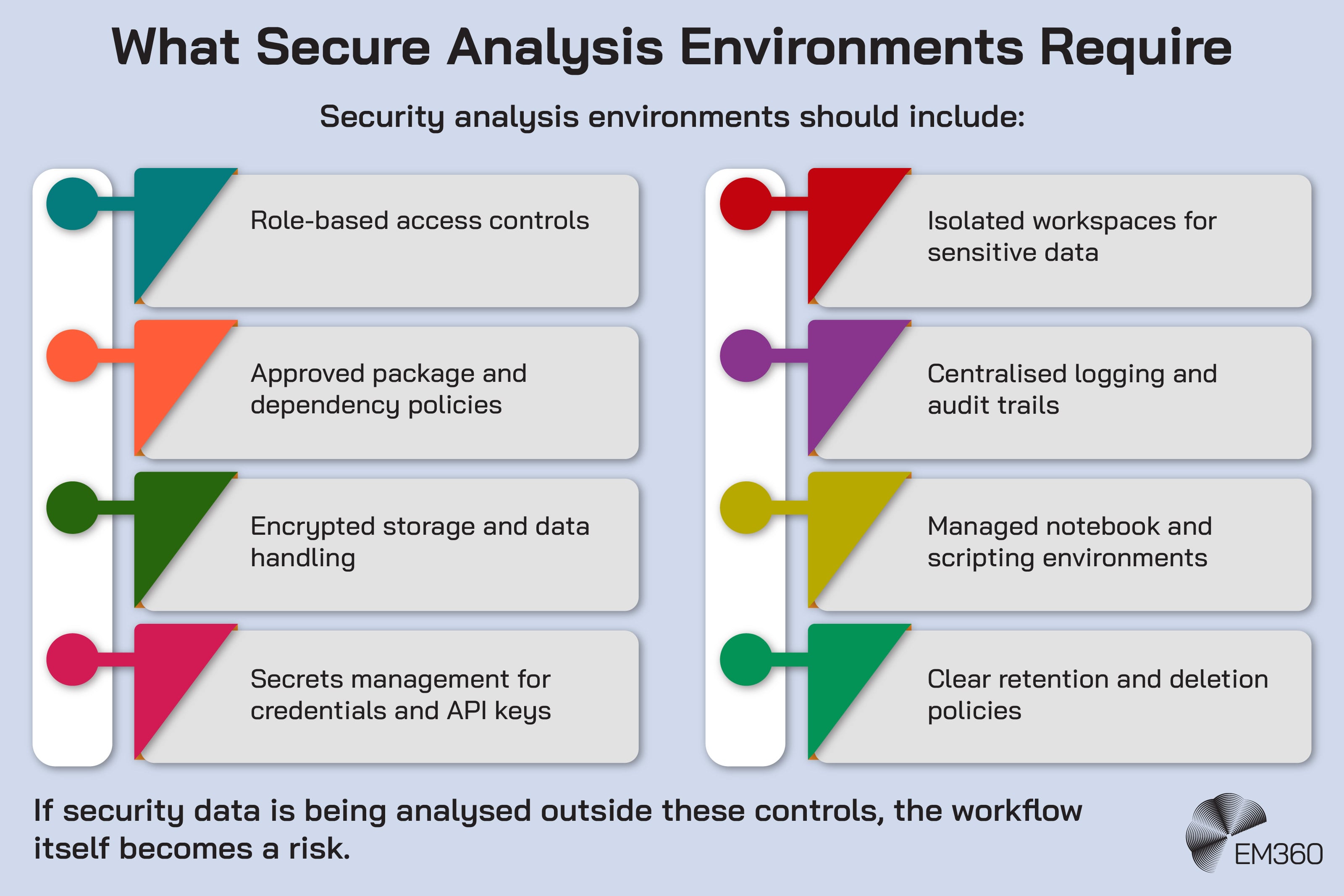
Put guardrails in place early
Governance always feels less exciting than capability. It's still what makes capability sustainable.
Access controls, environment management, package policies, notebook restrictions, secret handling, code review, and data retention rules should all be part of the conversation early. The same is true of platform choices. Python 3.14 officially supports free-threaded Python, and Python 3.13 introduced optional support through official installers.
That shows a runtime ecosystem still evolving, but operational maturity still matters more than chasing every new feature the week it appears.
Final Thoughts: Better Security Starts With Better Use Of Data
Security teams don't need more dashboards pretending to simplify reality. They need better ways to work with the data they already have.
That's where Python earns its keep. It helps teams clean messy inputs, add context, investigate faster, and turn ad hoc analysis into something more repeatable. It also fits the direction the industry is already moving in, where detection engineering, data fluency, and operational flexibility matter more than piling on more disconnected tools.
As identity-heavy attacks continue to rise and AI pushes both defenders and attackers to move faster, that ability to work with data directly will matter even more.
The organisations that get the most value here won't be the ones chasing the flashiest automation story. They will be the ones that combine practical analysis, clear guardrails, and a sharper understanding of where their security data is helping and where it's getting in the way.
If that's the shift your team is trying to make, EM360Tech’s cybersecurity coverage can help you think more clearly about the tools, trade-offs, and operating models that make it possible.







Comments ( 0 )