A malware dealer for two of Russia’s most dangerous cyber criminals has been unmasked after a “fatal mistake” led to researchers uncovering his identity.
The notorious hacker, codenamed ‘Jack’, is believed to be the mastermind behind Golden Chickens Malware as a Service (MaaS) provider – a malware suite used by financially-motivated cybercrime actors including Cobalt Group and FIN6.
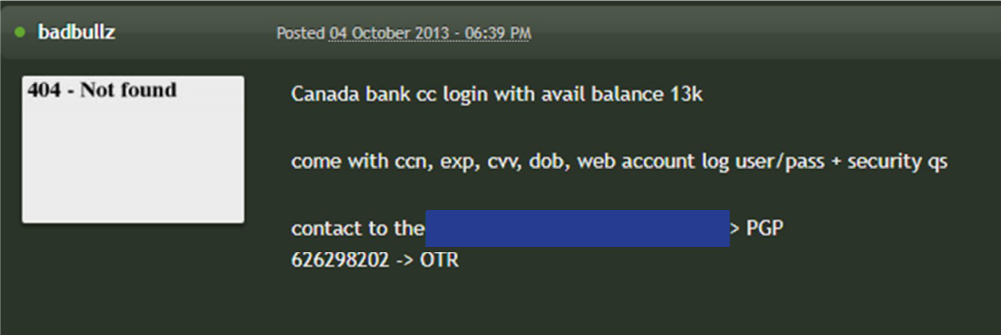
Jack’s identity was unearthed when digital investigators Joe Stewart and Keegan Keplinger found a forum post from one of Jack’s accomplices that included an account name for the encrypted chat service Jabber.
In a report posted on the eSentire website, Stewart and Keegan said the discovery “opened a flood of new accounts” after they found the Jabber account had been used to sell cybercrime tools across multiple other sites using different aliases attributed to other hackers.
One of the emails on these accounts had been used to sign up for Gravatar, the Automattic-owned service for creating online avatars, Stewart and Keegan explained.
By simply searching the email address on Gravatar, they uncovered what appeared to be a real name, which when googled uncovered a post from a security blog from the mid-2010s that confirmed the coder’s true identity.
"[Jack], who also shares the ‘Badbullz’ and ‘Badbullzvenom’ accounts with the Montreal-based cybercriminal 'Chuck,' made his fatal mistake when he used the Jabber account.”
"[He] has taken great pains to obfuscate the Golden Chickens malware, trying to make it undetectable by most companies, and strictly allowing only a small number of customers to buy access to the Golden Chickens MaaS.”
The researchers speculated that Jack brokered a deal with another hacker called ‘Chuck from Montreal’ so that he could post under Chuck's aliases on underground forums as a way to get around his notoriety as a malware ripper and keep his identity in the shadows.
"Like 'Chuck from Montreal,' Jack' uses multiple aliases for the underground forums, social media, and Jabber accounts, and he too has gone to great lengths to disguise himself," Stewart and Keplinger said.
"By using the ‘Badbullzvenom’ and ‘Badbullz’ accounts, he is essentially starting with a clean slate, and he can continue to build his credibility under the account aliases,” the researchers explained.
The life of a hacker
Putting together Jack’s digital trail, Stewart and Keplinger’s investigation traces Jack's progression from a teenager interested in building malicious programs to a longtime hacker involved in developing password stealers, crypters, and More_eggs.
Some of the earliest malware tools developed by Jack in 2008 consisted of Voyer, which is capable of harvesting a user's Yahoo! instant messages, and an information stealer christened FlyCatcher that can record keystrokes.
A year later, Jack released a new password stealer dubbed CON designed to siphon credentials from different web browsers and, VPN and FTP applications and now-defunct messaging apps like MSN Messenger and Yahoo! Messenger.
Then, in 2017 he released a separate tool called VenomKit, which has since evolved into the Golden Chickens MaaS.
The JavaScript malware is distributed via phishing campaigns and comes with several components to harvest financial information, perform lateral movement, and even drop a ransomware plugin for PureLocker called TerraCrypt.
To read more about Malware, visit our Business Continuity Page.
In recent years, Golden Chickens MaaS has caught the attention of some of Russia’s most dangerous customers for its ability to bypass security software.
First was Cobalt Group, a Russia-based cybercrime gang that used the service to hack 100 financial institutions across 40 countries, with single attacks raking in as much as $11 million,
Second was the also Russia-based Fin6, notorious for its large-scale strikes on the payments systems of retail and hospitality companies including British Airways and Ticketmaster.
A $200,000 bounty
Jack’s Golden Chickens malware-as-a-service continues to support cyber criminals today. eSentire said the malicious software had been used to target at least 11 companies since the start of 2022.
The cybersecurity firm said it also found the identities of his wife, mother, and two sisters. He and his wife are said to reside in Bucharest, Romania with his wife's social media accounts documenting their trips to cities like London, Paris, and Milan.

While the photos uncovered by Stewart and Kellingen appear to show a lavish lifestyle with designer clothing and accessories, the researchers note that Jack’s life may be in danger.
In 2018, a hacker using the name “Babay” said they had scammed to the tune of $1 million and offered $200,000 to anyone on the cybercrime forum Exploit.in who could uncloak Jack’s identity.
“The person scammed me, didn't complete his job, talks total nonsense, I can't contact him and he refuses to return the money back,” the hacker wrote. It remains unclear what they wanted to do once they’d acquired the coder’s name, or if their bounty remained active.
Though Stewart and Keplinger provided identifying information to Canadian law enforcement on the Chuck character, no charges have been announced yet, and the pair are unaware of authorities are actively investigating him based on their information
The pair are more hopeful law enforcement will act on their information about Jack, however, given his close ties to Russian cybercrime, it is unclear if they will purpose an arrest and put an end to criminal activities.












Comments ( 0 )