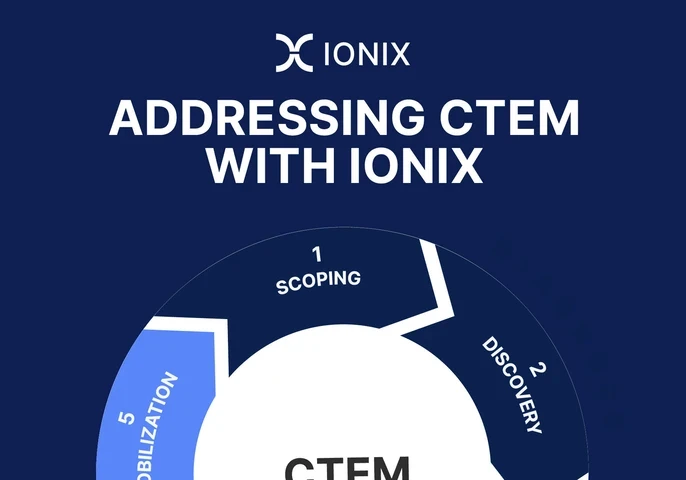
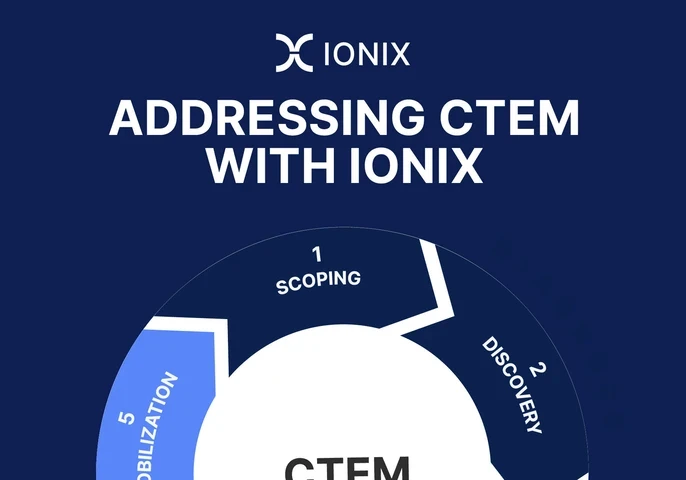
Addressing CTEM with IONIX
This episode of Don’t Panic! It’s Just Data explores the gap between AI ambition and organisational readiness, focusing on why many AI initiatives fail to move beyond early-stage pilots.

Discover expert led podcasts, articles, and news from enterprise technology leaders at EM360Tech, your source for B2B tech intelligence



“We are on the cusp of a breakthrough as we see its principles being applied to computing in ways that could transform the digital world” – Brian









Get the latest insights, analysis and tech news delivered straight to your inbox