Featured Whitepapers
The latest industry insights from our solutions providers
Latest in Enterprise Technology
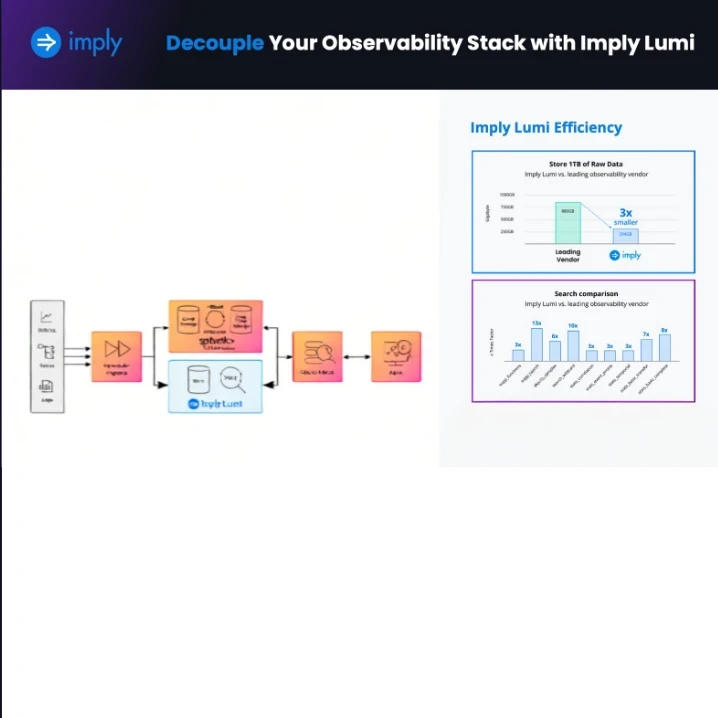
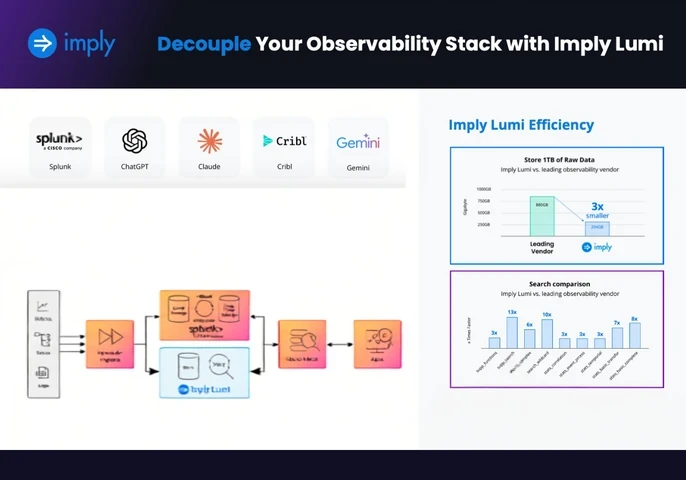
Decouple Your Observability Stack with Imply Lumi

How BTG Pactual Scales Security Investigations Without Replacing Splunk

Understanding the Cycle of Cybersecurity Control Configuration Risk
AI Agents for AML Reviews
SACR® AI SOC for MDR: The Structural Evolution of Managed Detection and Response

Empowering HR Teams To Become AI-savvy Talent Leaders