UK cybersecurity budgets set to surge over 30% in 2025

Infosecurity Europe report finds board level buy-in critical to building a safer cyber world

Discover expert led podcasts, articles, and news from enterprise technology leaders at EM360Tech, your source for B2B tech intelligence

Infosecurity Europe report finds board level buy-in critical to building a safer cyber world


Brand protection software helps organisations monitor, detect and address harmful risks online in order to protect their reputation.

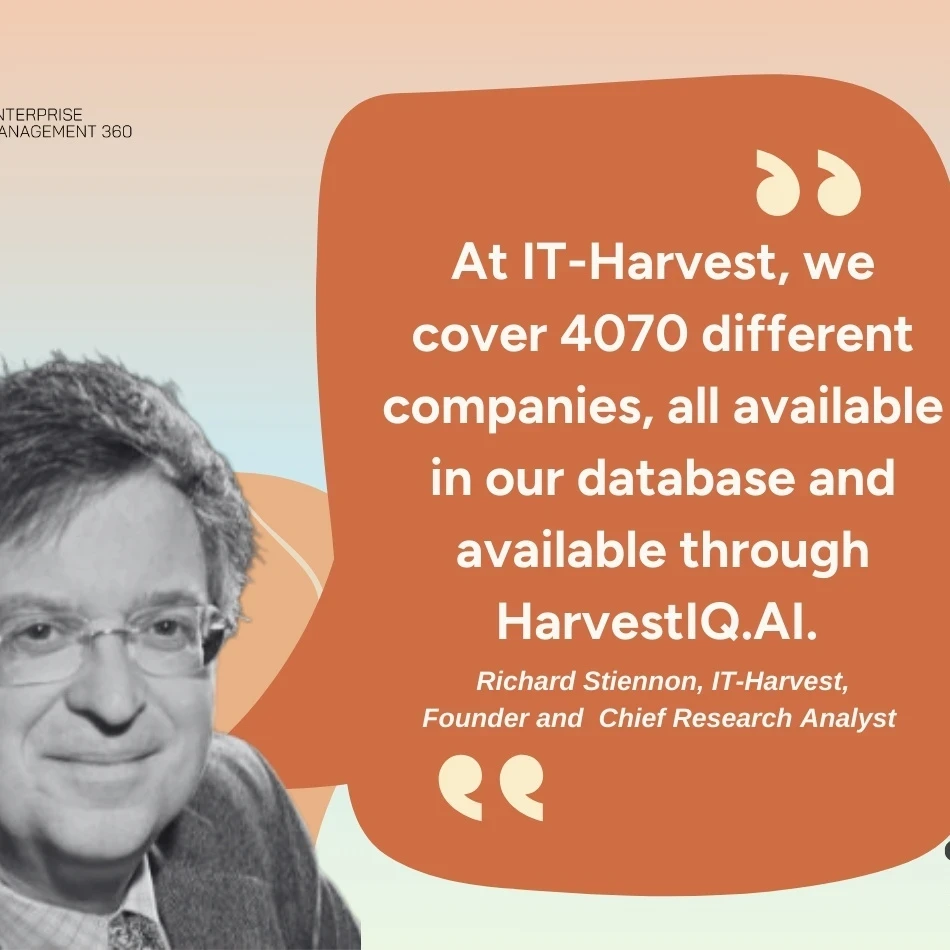
EM360Tech interviews Richard Stiennon, Chief Research Analyst at IT-Harvest on the company’s latest product called HarvestIQ.AI.







Get the latest insights, analysis and tech news delivered straight to your inbox