New software code is released almost as fast as new ideas are conceived in the tech industry. This makes web applications some of the most vulnerable places online, as these are exposed to the online world and easily targeted. The solution? Supporting technology.
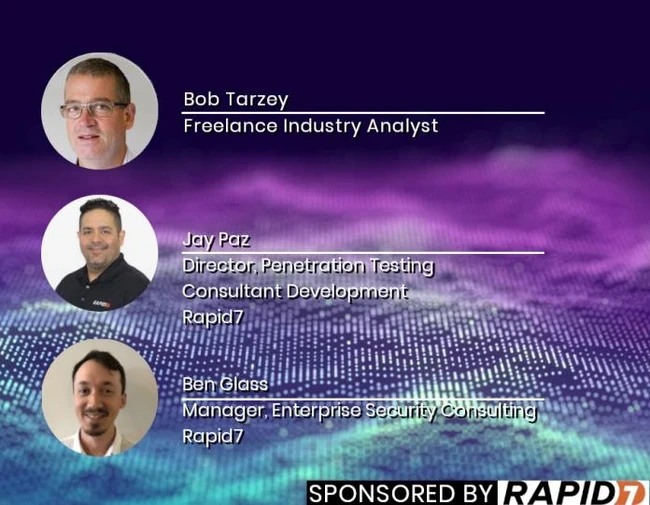
In the previous episode, Bob Tarzey spoke to Rapid7’s Ben Glass and Jay Paz, Manager of Enterprise Security Consulting and Director of Testing and Consultant Development, respectively, about building better code to stay secure. In this second podcast Bob, Jay and Ben look at some of the supporting technology to avoid vulnerability in companies. This includes the testing of code before releasing it, the testing of deployed software, and finding safer guides to build better and stronger software.







Comments ( 0 )