As lockdown extensions are issued across multiple nations, some of us sigh a breath of poignant solace. For those of us that can work remotely, there is an extent of relief in being told that we must stay at home, shielded from a virus that has populated nearly every continent (bar Antarctica).
However, despite the standstill that lockdowns present, the COVID-19 outbreak has proven that there truly is no rest for the wicked. The irony is that although we are isolating from visitors, we are at more risk of intruders and unwelcome guests than ever before.
Cybercriminals don’t stop for anything, and a global pandemic is no exception to the rule. While it’s worth pointing out that a small percentage of malicious actors have vowed to pause on healthcare cyber attacks at this time, an overwhelming majority of cybercriminals have instead upped the ante on their malicious endeavours.

This is to be expected, as the increase in digital dependency through remote working gives them plenty more opportunities to attack. However, the cyber attack landscape was already rife prior to the pandemic and widespread remote migration, with an attack occurring every 39 seconds on average. What’s more, the average time it took to identify a breach in 2019 was 206 days (and those are just the reported breaches). Thus, if remote working is going to exacerbate the cyber threat landscape, businesses have to be more proactive than ever to detect unwelcome guests and prevent them from hiding within the network.
Businesses are historically accustomed to a network perimeter approach to their cybersecurity. However, many cybersecurity professionals will attest that ensuring watertight security within the office walls is already no easy feat. Thus, it goes without saying that ensuring security throughout a work-from-home model is a new challenge entirely.
The security implications of working from home
In lockdown, entire workforces are operating on personal devices, and the associated challenges of this are many. Firstly, the geography alone introduces new attack vectors. When employees are away from the corporate office, they are also away from corporate IT security tools. These tools block employees from engaging in risky activity, including being routed to certain DNS domains or opening up potentially malicious files.
Remote working also takes away the ability of IT teams to directly oversee employees. With attacks more likely, the loss of control that comes with lack of oversight is a significant cause for concern. Not only are IT teams no longer able to be as proactive in protecting employees, but it also hinders their ability to mitigate insider threats. Internal actors are already responsible for 34% of data breaches, but the current circumstances could see that percentage rise due to the lack of intervention by IT teams.
Furthermore, employees’ personal devices will not have undergone any vetting by the IT teams to bolster protection and threat mitigation. In turn, employees, particularly those which are less security-savvy, become even more susceptible to infections and malware.
However, one of the most pressing problems of all comes from widening the pool of users with remote access. Granting employees access to your corporate network is, of course, non-negotiable to keep the business ticking over, but by casting a wider net of authorised users, it becomes difficult to determine whether access is legitimate or not.
With malicious actors trying to infiltrate your business at every turn, it’s imperative that organisations are proactive in trying to keep them out. Firewalls and endpoint solutions will simply not cut it alone, as many attack styles have outgrown them. Instead, organisations need to call in for reinforcement, and pronto.
When Remote Work Tests IDS
How mass telework exposed gaps in intrusion detection strategies and forced enterprises to rethink monitoring, data analysis and response.

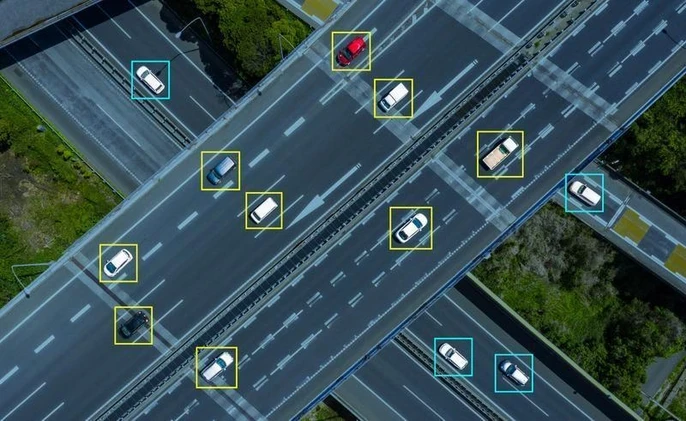
The nature of an attack is usually stealthy and sneaky, so it’s not enough to protect obvious entry points. It’s the places you’re not looking which are the most problematic – but if you don’t know where you need to be looking, how can you look for it? A highly effective remedy to the problem is to get full visibility. If you have eyes everywhere, then it’ll be far more difficult for attackers to get past you.
Accedian’s Skylight powered Security
With attacks growing in sophistication and evasive capabilities, businesses must exercise particular emphasis on detecting hackers and anomalous behaviour within their network. Next-generation intrusion detection systems (IDS) such as Accedian’s Skylight powered Security complements a business’s perimeter protection and provides them with full visibility over their network traffic.
IDS solutions monitor network traffic for suspicious behaviour and send alerts if such behaviour is detected. However, current generation IDS implementations have limitations in that they cannot always protect against sophisticated malware or unknown threats. Furthermore, over 80% of alerts by signature and policy-based IDS solutions are unreliable, which leads to resources being taken away from more critical alerts. With the case for a new approach being loud and clear, one was consequently delivered in behaviour-based, next-gen IDS solutions.
Next-gen IDS solutions harness intelligent data, and machine learning to power full network traffic analysis. In turn, offerings such as Skylight provide heightened visibility and round-the clock monitoring to quickly detect advanced cyber breaches and attacks that evade next-gen firewalls and antivirus software. Not only that, but Skylight will alert you to polymorphic malware and malware-free attacks that signature- and policy-based IDS solutions cannot proactively protect against.
Thus, next-gen IDS implementations are non-negotiable for organisations today, as they accommodate for the modern enterprise environment in a way that traditional tools cannot. As we see with Skylight, it caters towards all critical areas, including cloud, on-premises data centres, and the network edge, with open API and third-party tool integration capabilities, leaving very little scope for a successful attack. What’s more, its sensors are lightweight and cover all network topologies, including for cloud and hybrid environments, to detect malicious traffic across the entire physical and virtual attack surface.
Inside Cloud-Ready Operations
Sergio Bea outlines cloud migration practices and performance analytics that keep data centers responsive as networks and traffic patterns change.
As one of the many detections available in the Skylight arsenal, Accedian’s offering can scour through database transactions for possible SQL injections. If it detects any unusual or large database transfers, it quickly alerts SecOps teams, who will receive actionable intelligence and suggested steps for investigation if your teams deem it necessary.
Organisations can hit the ground running with Skylight. Its highly scalable architecture makes it perfect for elastic cloud and hybrid infrastructures, and it can be deployed in seconds. Given how ripe the conditions are for a cyber attack right now, every moment wasted can be costly, but Accedian’s offering can come to the rescue quickly.
Business continuity has become a particularly nerve-wracking topic as of late, but Accedian gives organisations the peace of mind they are seeking through their portfolio of best-in-breed solutions. Although it seems the odds are ever stacked in favour of the attacker (they only need to be successful once, remember), Accedian is challenging this by giving businesses full visibility, and therefore, full control.





Comments ( 0 )