In 2026, protecting data is no longer a back-office IT chore. It’s front-line defence for the enterprise. Data is everywhere, from cloud apps to personal devices to AI workflows, and threats move just as freely. The question isn’t whether you can recover from a breach, but whether you can prevent data loss in the first place.
Today’s enterprise data protection is proactive and continuous. It finds sensitive information across the business, secures it at the source, and stops leaks before they happen.
Why Enterprise Data Protection Looks Different in 2026
The shift isn’t subtle. Data now lives across cloud services, SaaS platforms, endpoints, email, and databases, and it moves fast because the business moves fast. Add AI tools and automated workflows into the mix and the old “protect the network and you’re done” mindset falls apart. Enterprise data protection in 2026 is about keeping sensitive information under control wherever it goes, and stopping leaks before they turn into incidents.
From perimeter controls to data-centric security models
For years, the perimeter did most of the heavy lifting. If you could keep attackers out of the network, you could keep the data safe. But cloud services, remote work, and AI-driven workflows have blurred that old boundary. So organisations are starting to focus on the data itself instead.
A data-centric security model treats sensitive data as though the rules are built into it. A file, database record, or report isn’t just “inside” or “outside” anymore. It’s protected with access controls, encryption, and audit trails wherever it lands. Even if something slips past network defences, the data still has guardrails around it. That’s what makes this model resilient.
Why discovery and classification come before protection
You can’t protect what you can’t find. That’s why data discovery and data classification now sit at the foundation of every serious protection strategy.
Sensitive data is scattered across collaboration tools, shared drives, cloud storage, data platforms, and employee devices. The first step is visibility. Where is it? What type is it? How sensitive is it? Once that’s clear, labels and context allow security controls to respond intelligently. A document marked as highly confidential shouldn’t leave the organisation unencrypted. A file tagged as internal might trigger a warning but not a hard block.
Discovery and classification turn data sprawl into something manageable. Skip this step and you get blind spots, overblocking, and false positives. Get it right and every other control becomes more precise.
The role of DLP in modern enterprise protection
Data Loss Prevention has evolved. It’s no longer just a rules engine scanning for keywords and blocking emails.
Modern enterprise DLP watches how data moves across endpoints, email, SaaS apps, and cloud storage. But it also looks at context. Who is moving the data? Is this normal behaviour for them? Is it part of their job?
Instead of acting like a blunt instrument, today’s DLP systems combine content inspection with identity and behaviour signals. They can coach users in real time, flag risky actions, or automatically block activity when the risk is clear. That shift matters. It reduces noise for security teams while preventing genuine data leakage before it escalates.
Data protection as an enabler for AI and automation
There’s a misconception that strong data protection slows innovation. In practice, the opposite is true.
AI systems and automation tools rely on data. Without guardrails, prompts, integrations, or automated workflows can easily exposed that data. Proactive data protection platforms extend policies into these environments. They can detect when sensitive information is about to be fed into an AI assistant and prevent it. They can apply encryption automatically. They can monitor unusual data flows triggered by automation scripts.
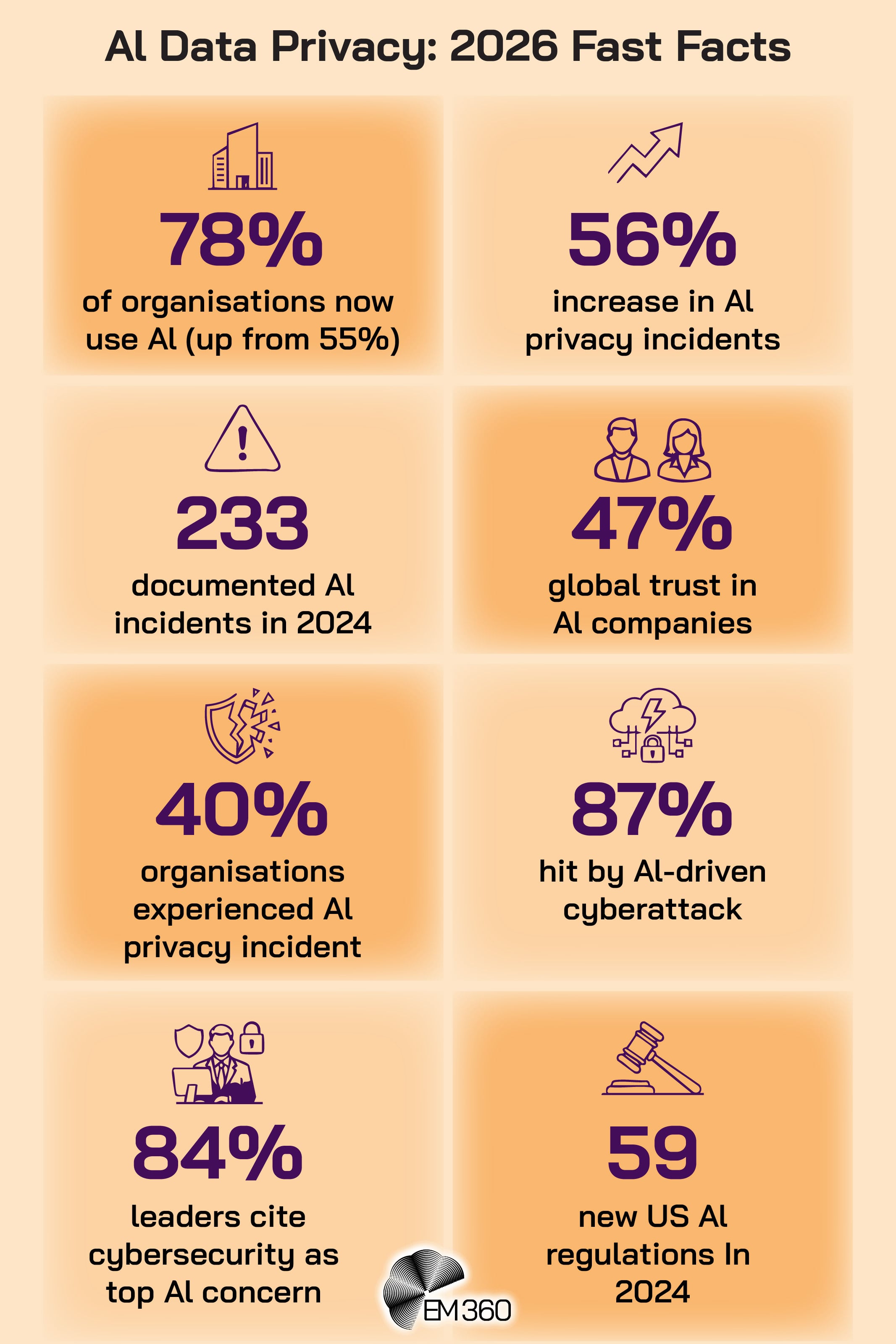
At the same time, protection itself is becoming more intelligent. AI-driven classification, anomaly detection, and automated policy enforcement reduce manual oversight and help security teams focus on more important tasks.
When data protection operates as a control layer across the organisation, leaders can move faster with less uncertainty. That confidence is what defines enterprise-ready security in 2026.
What to Look for in an Enterprise Data Protection Platform
A strong platform doesn’t win because it has the most features. It wins because it helps you answer three questions, quickly and with confidence: where is our sensitive data, who can touch it, and what happens when it starts moving in risky ways. If a tool can’t do that across cloud, SaaS, endpoints, and core data stores, it won’t hold up in a real enterprise environment.
At minimum, look for:
- Sensitive data discovery across all major repositories (on-prem databases, cloud storage, SaaS applications, endpoints). It should find where personal data, financial records, and other high-risk data is stored without you having to guess where to start.
- Data classification and labelling that tags data by sensitivity using patterns (like national ID numbers) and context, so policies can be applied consistently and not based on gut feel.
- Policy-driven encryption and tokenisation that protects files or data fields without breaking how people work. Key management matters here. Protection needs to stay with the data, not just the system it sits in.
- Data loss prevention (DLP) and content inspection across email, web uploads, cloud app activity, endpoints, and developer workflows. It should enforce policy in real time wherever data moves.
- User and entity behaviour analytics (UEBA) that flags unusual activity, like a user suddenly pulling far more sensitive data than normal. This adds context so you can tell the difference between normal work, a mistake, and a real threat.
- Integration hooks for workflow automation, such as sending events into your security tooling, triggering response playbooks, or applying labels and controls in the systems your teams already use. A platform that can’t connect cleanly will become a silo.
- Compliance reporting and audit logs that show what happened, who did it, and when, so you can support privacy and security requirements without manual evidence-chasing.
- Deployment options that match your reality, whether that’s cloud-native, on-prem, or hybrid, plus clean integration with identity providers, collaboration platforms, and the security stack you’ve already invested in.
- Enterprise-scale management with role-based controls, phased rollout support, and performance that holds up when you’re scanning and monitoring large volumes of data across the organisation.
Top Enterprise Data Protection Tools and Software
Below, we spotlight ten leading tools for proactive data protection in 2026. Each of these solutions brings unique strengths to an enterprise security stack. They help organisations discover sensitive data, prevent leaks, enforce policies, and stay compliant – all while minimising disruption to business.
Cyberhaven
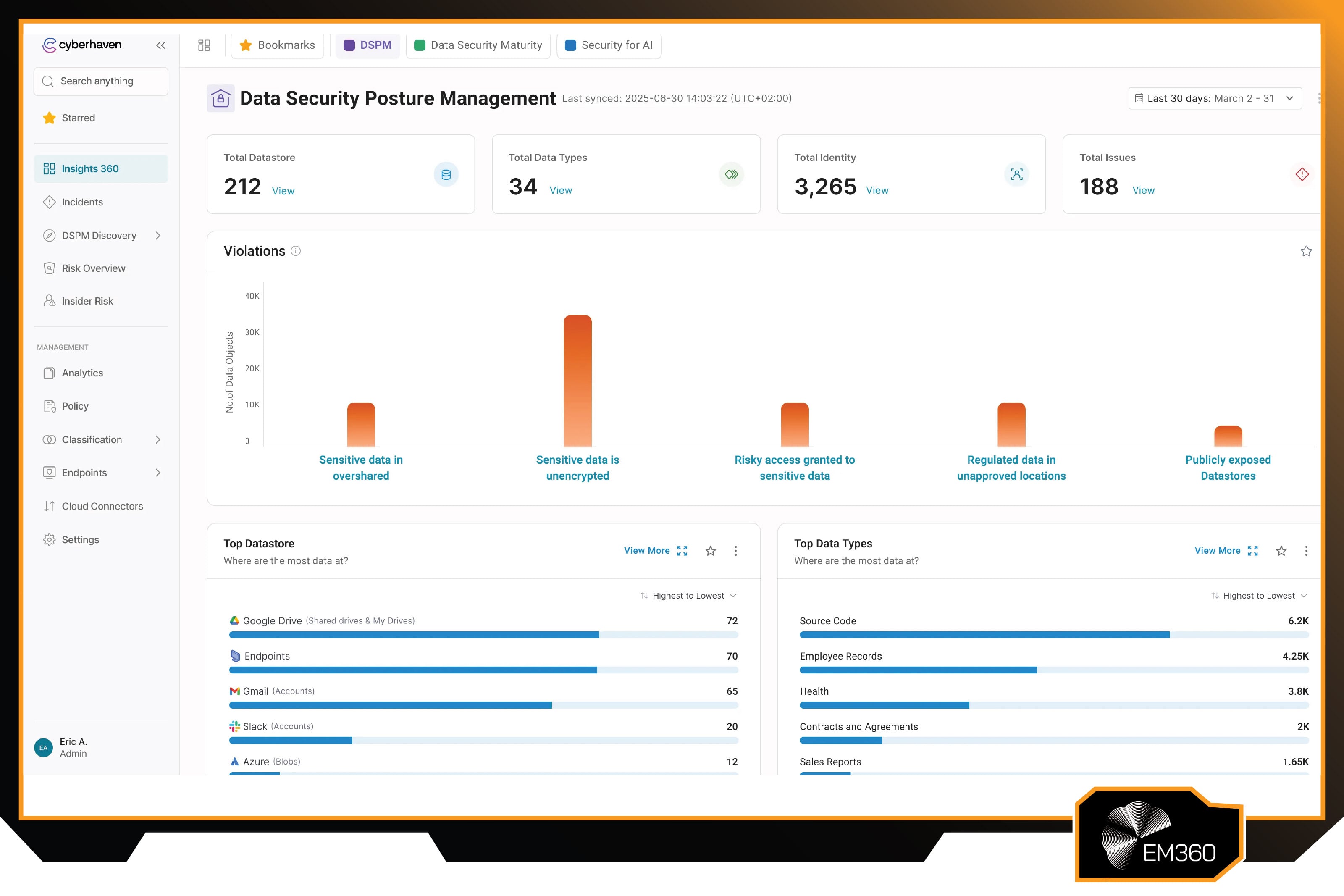
Cyberhaven is a data security company focused on protecting sensitive information as it moves across modern enterprise environments. The platform is built around the idea that understanding data flow is just as important as scanning data content, especially in organisations where work happens across cloud apps, endpoints, and fast-changing collaboration tools.
In recent years, Cyberhaven has positioned its approach around real-time visibility and response, aligning its platform with the way data is shared, copied, and reused across distributed teams and AI-enabled workflows.
Enterprise-ready features
Cyberhaven’s core strength is real-time data lineage, which tracks sensitive data as it flows through systems, applications, and user activity. That context means the platform doesn’t rely only on pattern matching.
It can understand where a piece of data came from, how it was handled, and where it’s going, which supports more accurate classification and more reliable policy enforcement. In practice, that helps reduce false positives and makes it easier to block genuinely risky movement, like sensitive files being pushed into unsanctioned apps or personal storage.
The platform is cloud-native and uses lightweight sensors to monitor and enforce controls across endpoints and cloud services without heavy on-prem infrastructure. It combines DLP, insider risk signals, and data security posture management into one operational view, with prebuilt policies and templates that can be tailored to how the business works.
When risky activity happens, Cyberhaven can respond in real time through user prompts, blocking actions, or alerting security teams, which supports proactive protection across common exfiltration paths like email, USB, cloud drives, and AI-assisted workflows.
Pros
- Tracks data flows and lineage for deep context, allowing precise policy enforcement.
- Cloud-based architecture with lightweight endpoint agents means faster deployment and updates.
- Reduces alert noise with intelligent classification, leading to fewer false positives.
- Unified platform covers DLP, insider risk, and DSPM, reducing the need for multiple tools.
- Provides real-time user feedback (pop-ups or warnings) to educate employees and prevent mistakes.
Cons
- Newer entrant compared to legacy DLP vendors, so in-house teams may require training to fully leverage advanced features.
- Heavy reliance on cloud services might not suit organisations with strict on-premise mandates or limited internet connectivity.
- The rich context collection could raise privacy considerations, requiring careful tuning of what user activity is logged.
Best for
Cyberhaven is best for large organisations dealing with sprawling data across cloud apps, endpoints, and AI platforms. It’s an excellent fit if you need to protect data in a highly dynamic environment. For example, tech companies or financial firms where sensitive data moves across many services quickly will benefit from Cyberhaven’s context-driven approach. Enterprises that want a next-gen DLP with strong insider threat capabilities and minimal noise will appreciate what Cyberhaven brings to the table.
Forcepoint DLP
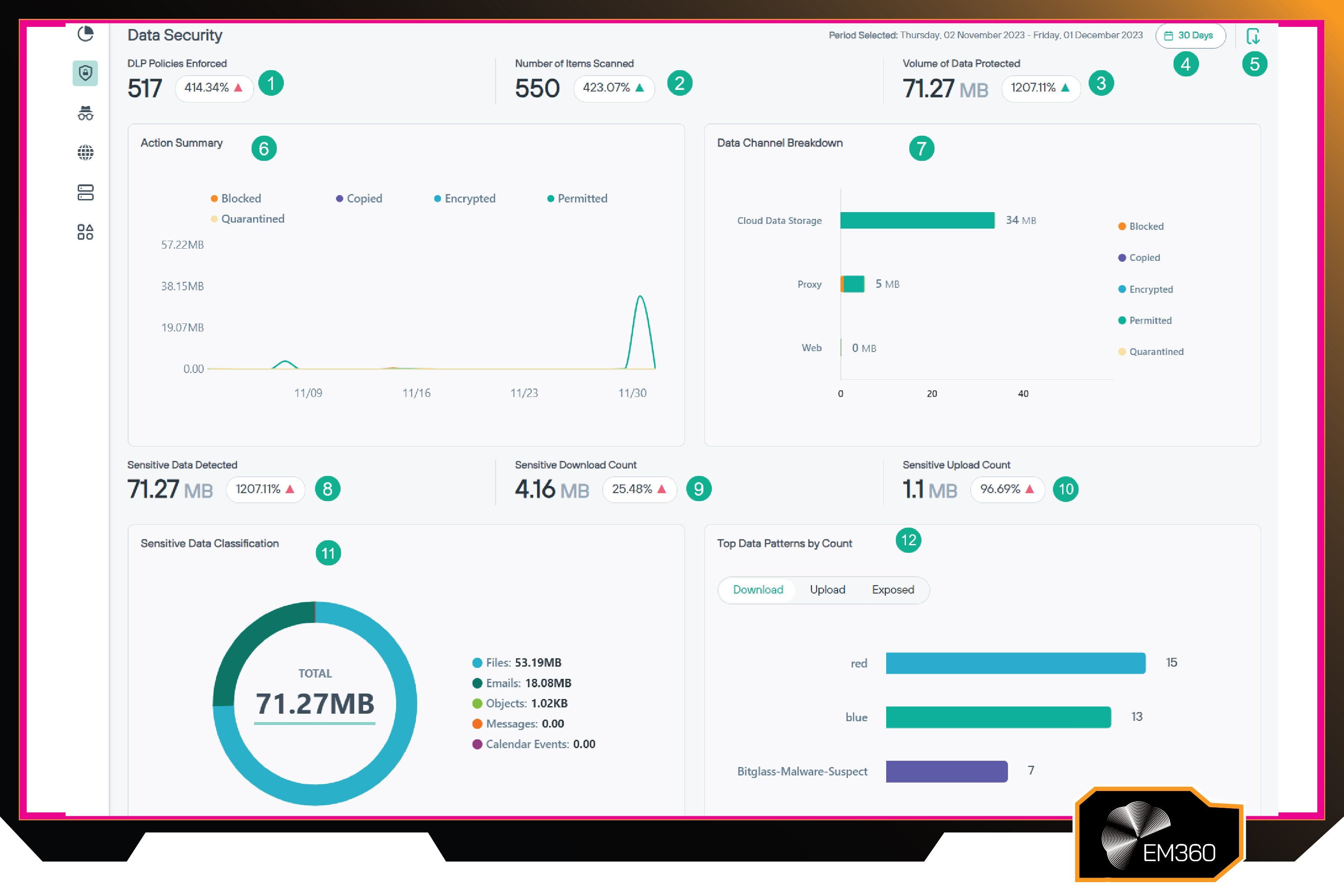
Forcepoint DLP is part of Forcepoint’s broader security portfolio and has been a long-running player in enterprise data loss prevention. The platform has evolved alongside the shift from perimeter-first security to data-centric controls, expanding from traditional network monitoring into endpoint and cloud coverage as enterprise data moved into SaaS and hybrid environments.
Today, Forcepoint positions DLP as a core control for protecting sensitive data across modern work patterns, where files, messages, and records move constantly between people, apps, and devices.
Enterprise-ready features
Forcepoint DLP is designed to protect data in motion, at rest, and in use by applying a consistent set of policies across key channels, including endpoints, network traffic, and cloud services.
It can monitor and control actions such as copying to removable media, printing, uploading to the web, and sending sensitive content through email, with coverage intended to follow the way data actually moves through an enterprise. This unified approach helps reduce policy gaps, so the same rules can apply whether data is leaving through a browser upload, a collaboration tool, or an endpoint action.
On the detection side, Forcepoint uses multiple methods to find sensitive content, including fingerprinting, pattern matching, and machine learning-assisted classification, alongside policy templates that support common regulatory needs.
It also includes behavioural signals to help determine when an action looks routine versus risky, and it supports flexible deployment models, including options that fit on-prem, cloud-delivered, and hybrid environments. The goal is to enforce protection in real time while giving security teams a single place to manage policies and investigate incidents.
Pros
- Proven DLP solution with comprehensive coverage of endpoint, network, and cloud channels.
- Robust policy library and templates for fast compliance with regulations (GDPR, PCI DSS, etc.).
- Advanced detection methods (fingerprinting, ML, OCR) catch sensitive data beyond simple keyword matching.
- Unified management console simplifies administration across thousands of users and multiple channels.
- Offers real-time blocking or user coaching, with flexibility to adapt enforcement based on risk level.
Cons
- Deployment and fine-tuning can be complex, especially on-premises components, requiring experienced administrators.
- Tends to be resource-intensive on endpoints if too many policies are active, which can impact device performance.
- As a feature-rich platform, smaller organisations might find they don’t use all capabilities, potentially making it a heavy investment.
Best for
Forcepoint DLP is ideal for enterprises that need a tried-and-true DLP solution with broad coverage. This includes financial institutions, healthcare organisations, or global corporations with diverse data channels. It’s particularly well-suited if you require granular control and have the security maturity to manage a sophisticated platform.
HashiCorp Vault
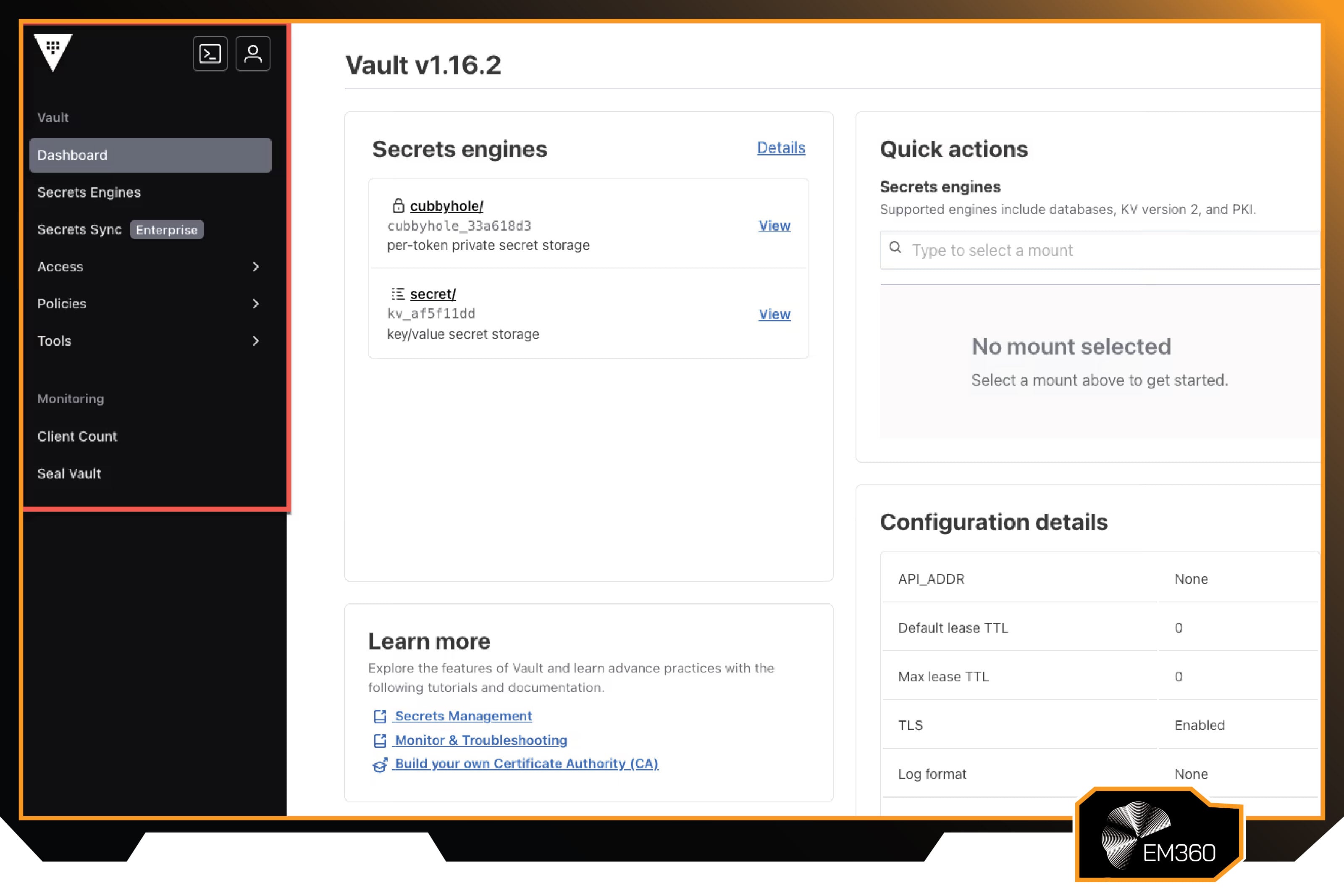
HashiCorp Vault is a secrets and encryption platform developed by HashiCorp and widely adopted across enterprise infrastructure and application environments. It’s built to solve a very specific problem: sensitive credentials and encryption keys don’t stay secure when they’re scattered across code, configuration files, and developer pipelines.
Over time, Vault has become a common backbone for organisations modernising their security posture, especially those working in cloud, DevOps, and automation-heavy environments where secure access and key control are non-negotiable.
Enterprise-ready features
Vault centralises the management of secrets such as API keys, passwords, and certificates, and controls how systems and users access them. Instead of long-lived credentials that get copied around and forgotten, Vault can issue short-lived, tightly scoped secrets and rotate them automatically.
Which reduces the value of stolen credentials. It also enforces strict access policies so applications and teams only get what they need, and it logs access in a way that supports audit and investigation.
Vault also supports encryption services by acting as a controlled layer for key management and cryptographic operations. Applications can encrypt and decrypt data through Vault under defined policies, which keeps keys out of application code and reduces key sprawl across the environment.
For enterprise deployments, Vault supports high availability, replication, and integration with hardware security modules and cloud key services, and it offers APIs and plugins so it can fit into existing toolchains. While it isn’t a DLP tool, it plays a direct role in proactive data protection by reducing secret leakage and enforcing secure encryption at scale.
Pros
- Excellent secret management eliminates embedded passwords/keys in code by providing dynamic, short-lived credentials.
- Centralises encryption keys and provides consistent, audited encryption services for applications.
- Highly integrable via API, with broad community and DevOps tool support.
- Enterprise version supports high availability and multi-datacenter replication, ensuring secrets are available securely wherever needed.
- Strengthens overall security posture by enforcing least privilege access to data and secrets.
Cons
- Not a turnkey “point-and-click” solution. It requires DevOps and security engineering effort to integrate into systems and workflows.
- Primarily focused on infrastructure and application-level data protection, so it doesn’t address content-based data loss (Vault won’t stop someone emailing a file, for example).
- Improperly configured Vault can become a single point of failure (if too restrictive, it could hinder operations; if too open, it undermines security).
Best for
HashiCorp Vault is best for enterprises that are pursuing a “secure-by-design” strategy – organisations heavily leveraging cloud infrastructure, microservices, and DevOps practices. Think of tech firms, SaaS providers, or any company that builds software and needs to manage secrets and encryption at scale. It’s also valuable in regulated industries (finance, healthcare) where controlling access to encryption keys and maintaining audit trails are mandatory.
IBM Guardium Data Protection
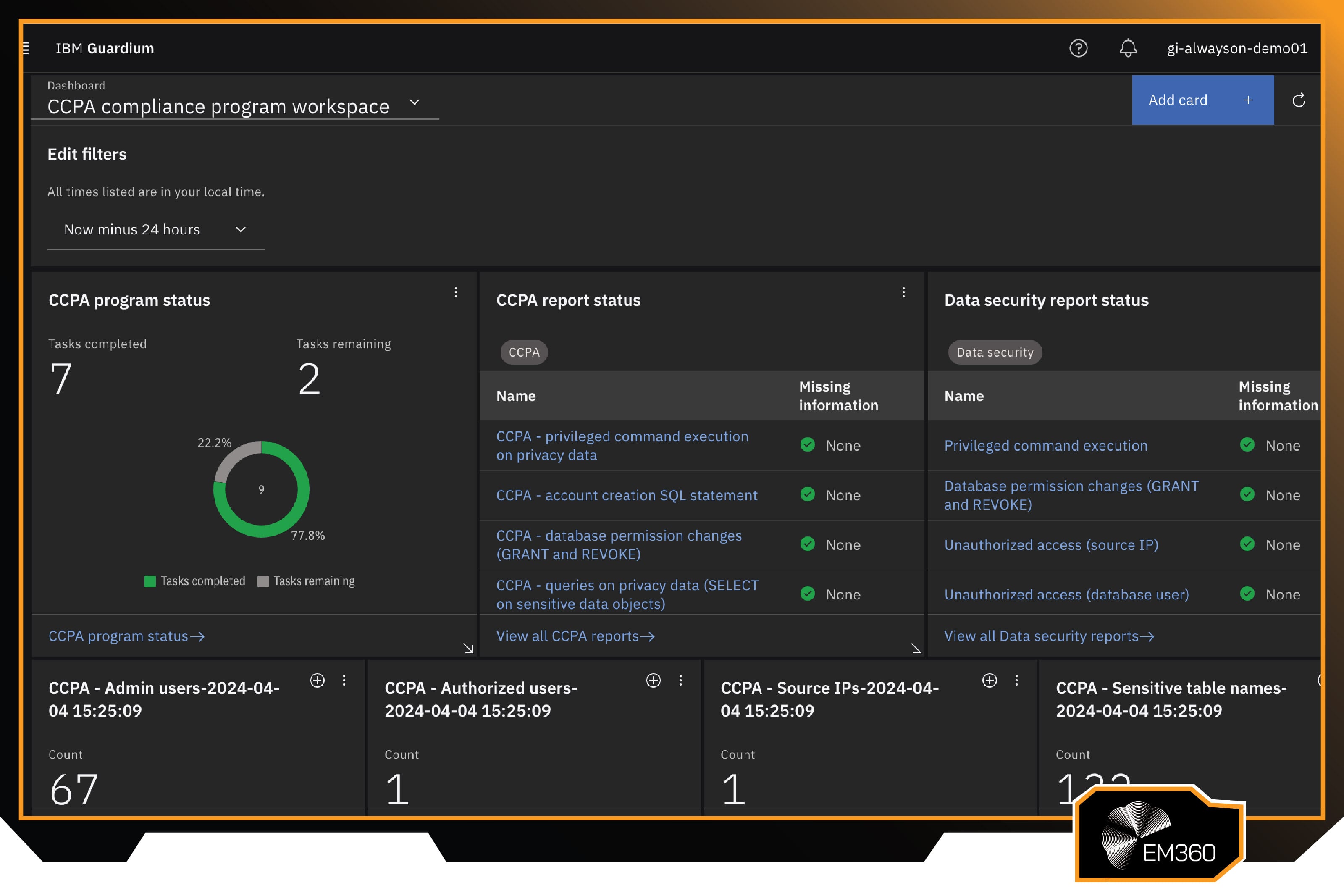
IBM Guardium Data Protection is part of IBM’s Guardium portfolio, built to help enterprises protect sensitive data where it often matters most: databases and large-scale data platforms. The platform has a long history in environments where governance, auditability, and strict control over data access are business-critical, including finance, healthcare, and large regulated enterprises.
As data estates became more hybrid and complex, Guardium expanded from database activity monitoring into broader discovery and policy enforcement capabilities that support modern compliance and risk management needs.
Enterprise-ready features
Guardium is designed to discover and classify sensitive data within databases and data stores, monitor access activity, and enforce policies that reduce misuse and leakage. It can provide visibility into who accessed what data, when, and how, and it can detect and respond to risky or unauthorised actions in near real time.
Guardium also supports controls such as masking and policy-based restrictions, helping organisations reduce exposure while still allowing legitimate work to continue. The platform includes compliance reporting and audit-ready logging to support regulatory requirements, with templates and controls that map to common standards.
It can operate across hybrid environments, supporting both on-prem and cloud data stores, and it’s built to scale for high-volume enterprise use cases. Guardium also integrates into broader security operations by feeding data access insights into monitoring and response workflows, which helps teams connect “data activity” to the bigger security picture without treating databases as a separate world.
Pros
- Specialised in database and structured data security, providing deep visibility into who is accessing what data and how.
- Real-time blocking, masking, or alerting on policy violations at the data source, which stops breaches at the earliest point.
- Strong compliance features (pre-built rules, reports) that simplify audits and help maintain standards across diverse data stores.
- Scales for large enterprises, proven in mission-critical, high-volume database environments.
- Offers both agent-based and network-based monitoring options, giving flexibility in how to deploy with minimal performance impact.
Cons
- Focuses mainly on databases and structured repositories; unstructured file data protection might require additional IBM modules or other tools.
- Deployment and tuning can be complex. Installing agents or network taps for multiple databases requires careful planning and cooperation with DBAs.
- The user interface and reporting, while powerful, can feel geared toward specialised security analysts, which may steepen the learning curve for new teams.
Best for
IBM Guardium Data Protection is best for large enterprises with significant structured data assets – such as banks, insurance companies, healthcare networks, or retail companies with vast customer databases. It’s ideal for organisations that already have a strong data governance culture and need to enforce policies tightly for compliance and security, especially in hybrid cloud scenarios where the same solution must cover on-prem and cloud databases seamlessly.
Microsoft Purview
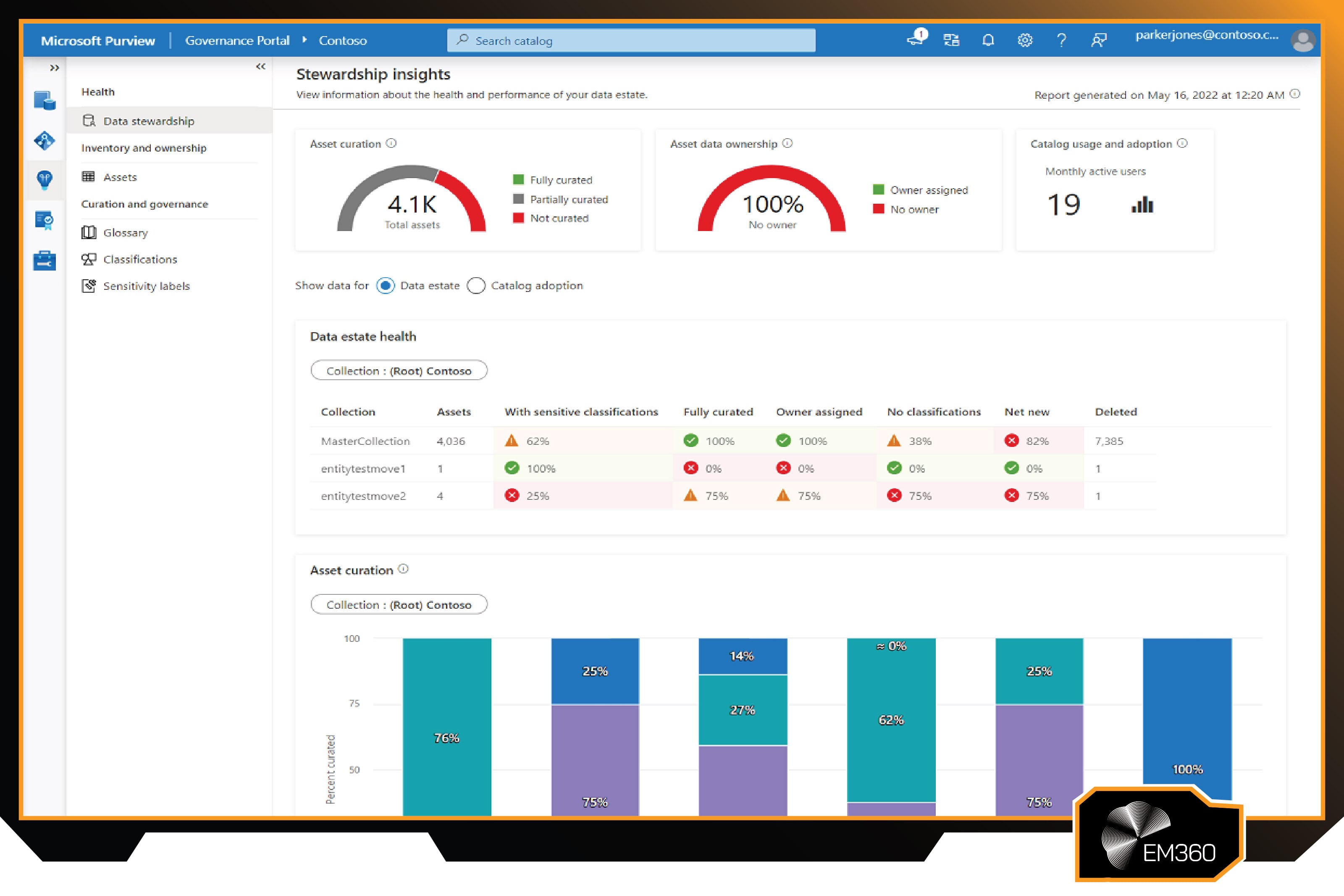
Microsoft Purview is part of Microsoft’s broader security, compliance, and data governance portfolio, built to help organisations understand, manage, and protect data across Microsoft services and connected environments. Over time, Purview has grown from a governance and compliance foundation into a more unified set of controls that support modern enterprise needs.
Especially as Microsoft 365 became the default workspace for many organisations. Today, it sits at the point where governance meets enforcement, tying classification, policy, and protection to how people actually work in Microsoft’s cloud ecosystem.
Enterprise-ready features
Purview brings together sensitivity labelling, information protection, and DLP so organisations can classify data and apply controls that travel with it. Labels can trigger encryption and access restrictions, which means a document can remain protected even when it’s shared or moved beyond its original location.
The platform also supports automated classification through built-in sensitive information types and trainable classifiers, helping teams apply consistent protection at scale without relying on every user to label everything perfectly.
Purview’s DLP coverage spans key Microsoft channels, including Exchange email, SharePoint, OneDrive, Teams, and Windows endpoints, allowing one policy set to control multiple data paths. It also includes insider risk capabilities and broader integration through connectors, which helps extend oversight beyond Microsoft-only environments where needed.
For organisations already using Microsoft 365, deployment can be streamlined through licensing and central administration, keeping governance and protection managed from the same place rather than spread across separate tools.
Pros
- Natively integrated with Microsoft 365 services, providing seamless protection for emails, files, and chats without additional agents.
- Sensitivity labels with built-in encryption persist with the data, ensuring protection travels with the file.
- Rich set of pre-built sensitive information types and trainable classifiers leverage Microsoft’s AI to auto-detect a wide range of data categories.
- Easy for Microsoft-centric IT teams to adopt, with a unified compliance portal and continuous updates from Microsoft (no complex upgrades to manage).
- Provides insider risk tools and compliance monitoring out of the box, complementing DLP with broader governance insight.
Cons
- Best features require higher-end Microsoft licensing (E5 or equivalent add-ons), which can be costly if you’re only after specific capabilities.
- If your environment isn’t mostly Microsoft (e.g., using Google Workspace or various non-Microsoft apps), Purview’s coverage of third-party systems is more limited and may need additional integration effort.
- Some advanced configurations (like custom sensitive info types or complex DLP rules) can be tricky, and you might need to align with Microsoft’s cloud way of doing things rather than fully bespoke policies.
Best for
Microsoft Purview is a top choice for organisations deeply invested in the Microsoft ecosystem. If your employees live in Outlook, SharePoint, Teams, and Windows, Purview provides unparalleled visibility and control with minimal friction. It’s particularly suitable for mid-to-large enterprises that want to merge data protection with compliance and leverage cloud intelligence.
PKWARE Smartcrypt
PKWARE Smartcrypt is part of PKWARE’s data protection portfolio and builds on the company’s long history in file technologies and encryption. Positioned as a data-centric protection solution, Smartcrypt focuses on identifying sensitive data and securing it through encryption and controlled access, rather than relying only on perimeter controls.
It’s designed to support organisations that need consistent protection across mixed environments, including legacy systems, where sensitive files still exist far outside modern cloud platforms.
Enterprise-ready features
Smartcrypt combines discovery and classification with policy-driven encryption, helping organisations locate sensitive files across endpoints, servers, and wider enterprise infrastructure and then protect them in place.
Once data is identified, encryption can be applied automatically based on policy, which keeps protection tied to the file rather than the location. That approach reduces risk when files move through email, shared drives, portable media, or other common enterprise paths where data can leak through routine workflows.
Centralised key management supports controlled access, so authorised users and applications can decrypt data while everyone else is locked out. Smartcrypt also supports masking and redaction for cases where data needs to be sanitised rather than simply encrypted, which can help with privacy and governance needs.
Its cross-platform support makes it relevant for organisations that need encryption and control across both modern endpoints and older platforms that still carry sensitive operational and customer data.
Pros
- Combines data discovery with automatic encryption, ensuring sensitive data is protected as soon as it’s identified.
- Persistent file encryption means data remains secure even outside the corporate network or if copied to unmanaged devices.
- Centralised key management and policy control give admins fine-grained oversight of who can decrypt what.
- Platform-agnostic support (from desktops to servers to mainframes) covers legacy systems that many modern tools overlook.
- Can fulfil privacy requirements by masking or encrypting personal data on the fly, helping with compliance for regulations like GDPR.
Cons
- Users or applications must have Smartcrypt (or its reader) to read encrypted data, which requires deployment and might cause collaboration hurdles if external parties are involved.
- The approach relies on strong internal policy design. If policies are too broad, you could end up encrypting everything and causing inconvenience; too narrow and some data might slip through unprotected.
- Organisations with existing heavy investments in other DLP/DRM solutions might find overlap, and careful integration is needed to avoid conflicts between systems.
Best for
PKWARE Smartcrypt is a great fit for industries like finance, government, and healthcare – where leaking a single file can be catastrophic. They will appreciate the belt-and-braces approach of encrypting data by default. It’s also well-suited for enterprises with heterogeneous IT environments (including legacy platforms) since Smartcrypt can cover those. If your strategy assumes that every piece of sensitive data will travel and thus must protect itself, Smartcrypt aligns perfectly by making encryption and protection automatic and ubiquitous.
Proofpoint Enterprise DLP

Proofpoint Enterprise DLP is part of Proofpoint’s broader people-centric security portfolio, with roots in email security and a strong focus on protecting organisations from human-driven risk. As enterprise work shifted into cloud services and collaboration platforms, Proofpoint expanded DLP into a more unified approach across email, endpoints, and cloud apps.
It’s designed for organisations that want DLP controls that don’t just detect sensitive content, but also interpret user behaviour and intent, especially in environments where insider risk is a real concern.
Enterprise-ready features
Proofpoint delivers DLP across high-risk channels including email, endpoints, and cloud services, with a strong emphasis on user context and incident correlation. It can detect sensitive data leaving the organisation through common routes and apply enforcement actions like blocking, encryption, or user prompts based on policy.
Because Proofpoint’s wider platform includes threat intelligence and messaging security, DLP incidents can be viewed alongside other signals that help teams understand whether a data event is a mistake, a policy gap, or part of a broader attack pattern.
The platform also supports insider threat workflows through integrated monitoring and investigation features, giving security teams richer context around risky behaviour over time. Pre-built policies, classifiers, and integration options help scale protection across large organisations without starting from scratch.
While centralised incident management supports triage and response. The result is a DLP approach that’s not just about stopping a single outbound action, but about identifying patterns that lead to data leakage and intervening early.
Pros
- Comprehensive coverage with a people-centric lens, correlating email, cloud, and endpoint events to paint a full picture of data use.
- Strong insider threat focus. It can capture screenshots or video of user actions, aiding investigations and deterring malicious behaviour.
- Proven email DLP capabilities (historically a blind spot for some DLP tools) thanks to Proofpoint’s expertise in messaging security.
- Cloud-ready, with CASB integration to protect data in popular SaaS apps and to monitor user actions within those apps.
- Flexible policy engine and library, including recognition of third-party classification tags, which eases integration into existing data governance frameworks.
Cons
- The endpoint agent, due to its extensive monitoring (down to screen capture), can raise privacy concerns and must be deployed carefully to comply with privacy laws and maintain employee trust.
- Correlating signals from multiple channels makes the system powerful but also complex to administer; extracting full value may require skilled analysts and fine-tuning.
- Proofpoint’s solution is often part of a larger ecosystem – best results come if you also use its email security and cloud security products, which could be a heavy investment if you’re not already in the Proofpoint portfolio.
Best for
Proofpoint Enterprise DLP is best for organisations that prioritise insider threat detection and comprehensive data oversight. This includes industries like legal, defence, or tech, where specific intellectual property needs guarding and user behaviour might be as important to monitor as content itself. It’s a great choice for companies that have experienced insider data misuse or are highly targeted by external social engineering attacks, as it ties data protection closely with human behavior patterns and threat intelligence.
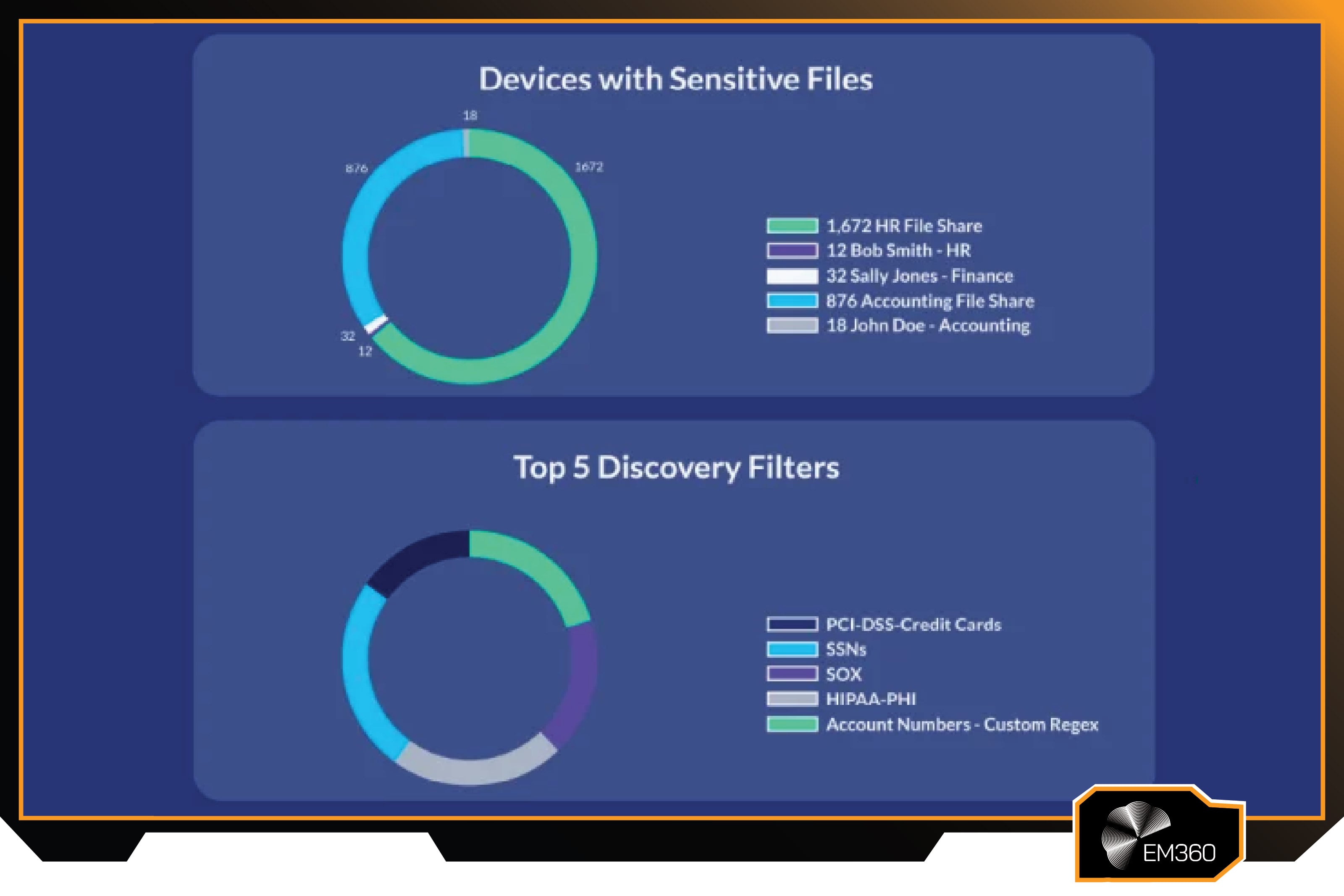
Spirion Sensitive Data Manager

Spirion Sensitive Data Manager is part of Spirion’s broader data discovery and privacy protection offering, built to help organisations locate and control sensitive data that’s been left behind in everyday systems. The platform is known for focusing on what many enterprises struggle to see clearly: sensitive information sitting across endpoints, file shares, databases, and cloud storage, often outside formal governance processes.
Over time, Spirion has positioned itself as a specialist in sensitive data discovery and remediation, supporting organisations that need stronger privacy controls, clearer data accountability, and fewer hidden exposures.
Enterprise-ready features
Spirion is designed to discover and classify sensitive data across a wide range of locations, with a strong emphasis on accuracy so teams aren’t buried under noisy scan results. Its scanning capabilities cover common enterprise data stores, and it can identify sensitive information such as personal identifiers, financial data, and health-related records.
Which helps with building a clear inventory of where high-risk data exists. That visibility supports better prioritisation, because teams can focus on the most exposed data first rather than treating every file as equally urgent.
Once sensitive data is found, Spirion supports remediation workflows that help reduce risk rather than simply report on it. It can trigger actions such as quarantining or deleting files, masking data, and routing ownership decisions to the right people, which helps spread accountability beyond IT.
It also provides executive-level reporting to show progress and risk reduction over time, and it supports ongoing scanning so new exposures are caught as they appear, not months after the fact.
Pros
- High-accuracy scanning and pattern matching yields fewer false positives, so teams can trust and act on the discovered data.
- Comprehensive visibility into both structured and unstructured data locations, leaving few places for sensitive data to hide.
- Allows automated or guided remediation (quarantine, deletion, etc.), not just read-only reports, thereby directly reducing risk.
- Flexible deployment (SaaS or on-prem) and ability to scale scans enterprise-wide with central management.
- Strong for compliance – helps demonstrate due diligence in finding and securing personal data, which is key for GDPR, CCPA and similar regulations.
Cons
- Because it’s focused on data at rest, it doesn’t prevent real-time data exfiltration; it’s best used alongside DLP solutions for a complete strategy.
- Initial scans in a large environment can be time-consuming. Crawling through terabytes of data might take a while and needs to be scheduled carefully to avoid disrupting business operations.
- Users responsible for data might feel overwhelmed by remediation tasks if not properly guided. An organisation should pair Spirion’s findings with clear processes and support for data owners.
Best for
Spirion Sensitive Data Manager is ideal for organisations that need to deeply understand and control their sensitive data inventory. This often includes those in finance, healthcare, higher education, or government – environments with lots of personal data scattered in documents and databases. If your enterprise is concerned that sensitive information is stored in unknown places (e.g., old files on employees’ machines or unmanaged cloud folders), Spirion provides the means to reveal it and deal with it.
Symantec Data Loss Prevention
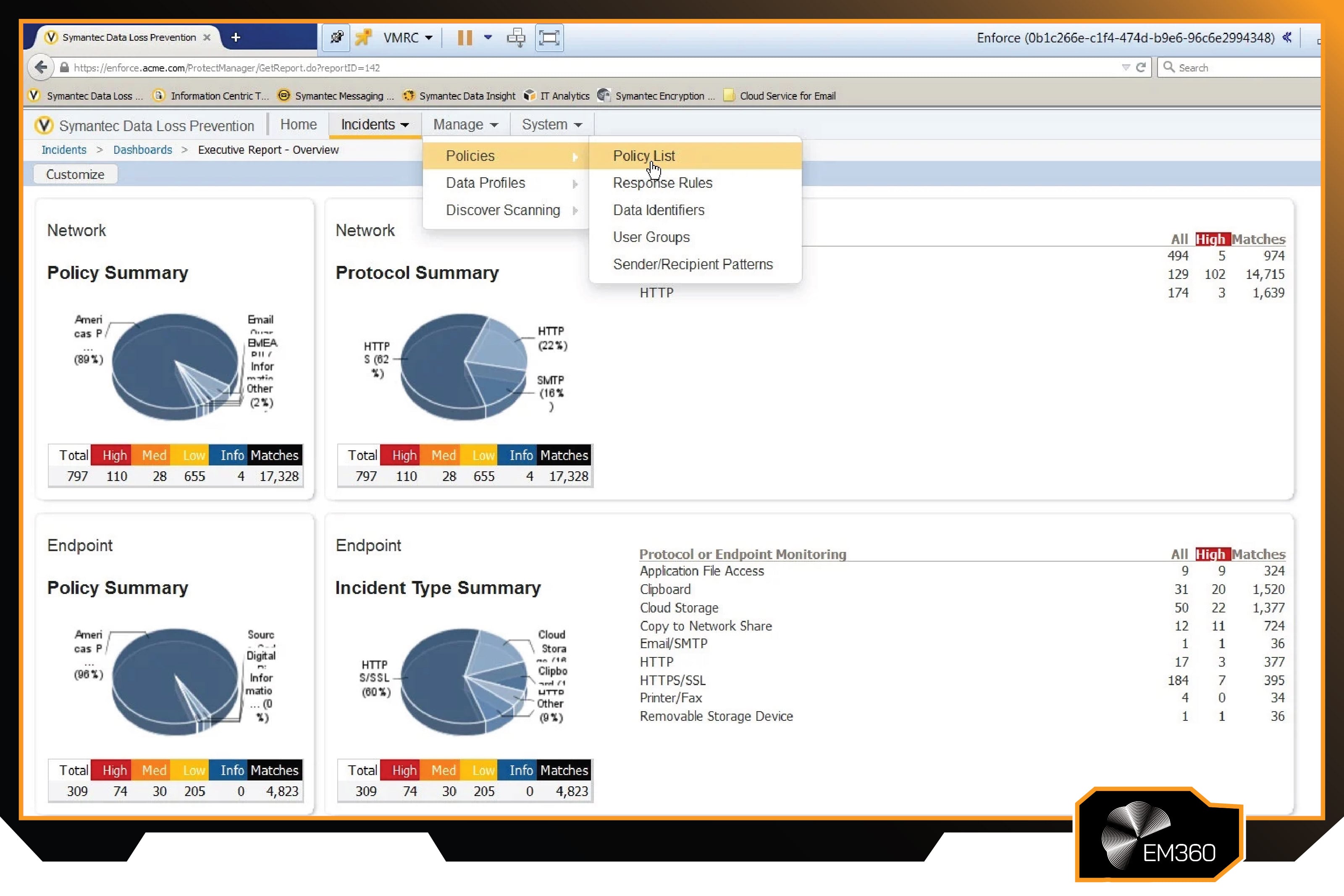
Symantec Data Loss Prevention is part of Broadcom’s enterprise security portfolio and has been a long-standing DLP platform in large, complex organisations. Over the years, it has built a reputation for deep policy control and broad coverage across common data loss channels, which is why it remains widely recognised in enterprise DLP programmes.
Its approach is shaped by long experience in regulated industries where detection accuracy, detailed workflows, and audit-ready reporting are essential, not optional.
Enterprise-ready features
Symantec DLP is designed to detect and control sensitive data movement across major vectors including endpoints, network traffic, storage repositories, and cloud-connected services. It supports multiple detection methods, including pattern matching, exact data matching, and content recognition techniques that help it identify sensitive information in different formats.
Including cases where data is embedded in images or structured records. This breadth allows enterprises to apply consistent policies across the most common ways data leaves an organisation, from email and uploads to copying and local device actions.
The platform also supports centralised policy management and incident workflow, which helps teams move beyond detection into repeatable response. Enforcement can include blocking, user notification, escalation into investigation queues, and integration with encryption workflows to secure data rather than simply stop activity.
For larger organisations, role-based administration and scalable architecture support enterprise operations across many locations and user groups, while maintaining the reporting and audit trails needed for compliance and governance.
Pros
- Highly granular and powerful detection technologies catch a wide array of data types, even in complex or obfuscated scenarios.
- Comprehensive channel coverage (endpoint, email, web, cloud, storage) under a unified policy framework ensures consistent enforcement.
- Mature incident management and reporting features that enterprises have relied on for years to drive remediation and measure risk reduction.
- Large user community and knowledge base, given its long presence, which can be helpful for deployment and troubleshooting.
- Can integrate with other Broadcom (Symantec) security products, like their CASB or endpoint protection, to enhance overall security orchestration.
Cons
- Initial deployment is significant. It requires planning to deploy multiple servers and agents, and careful tuning of policies to avoid a flood of alerts.
- The interface and user experience can seem dated compared to newer competitors; some tasks might require more clicks or deeper expertise.
- Broadcom’s acquisition led to changes in support and release cadence that some customers found challenging. It’s worth evaluating the current support model and roadmap if considering this solution.
Best for
Symantec Data Loss Prevention is best suited to large enterprises that need a mature, highly customisable DLP solution. It fits organisations with strict regulatory requirements and complex environments that span both legacy infrastructure and modern cloud services. For teams with the resources to manage a detailed policy framework, Symantec offers deep control and broad coverage across data channels.
Varonis Data Security Platform
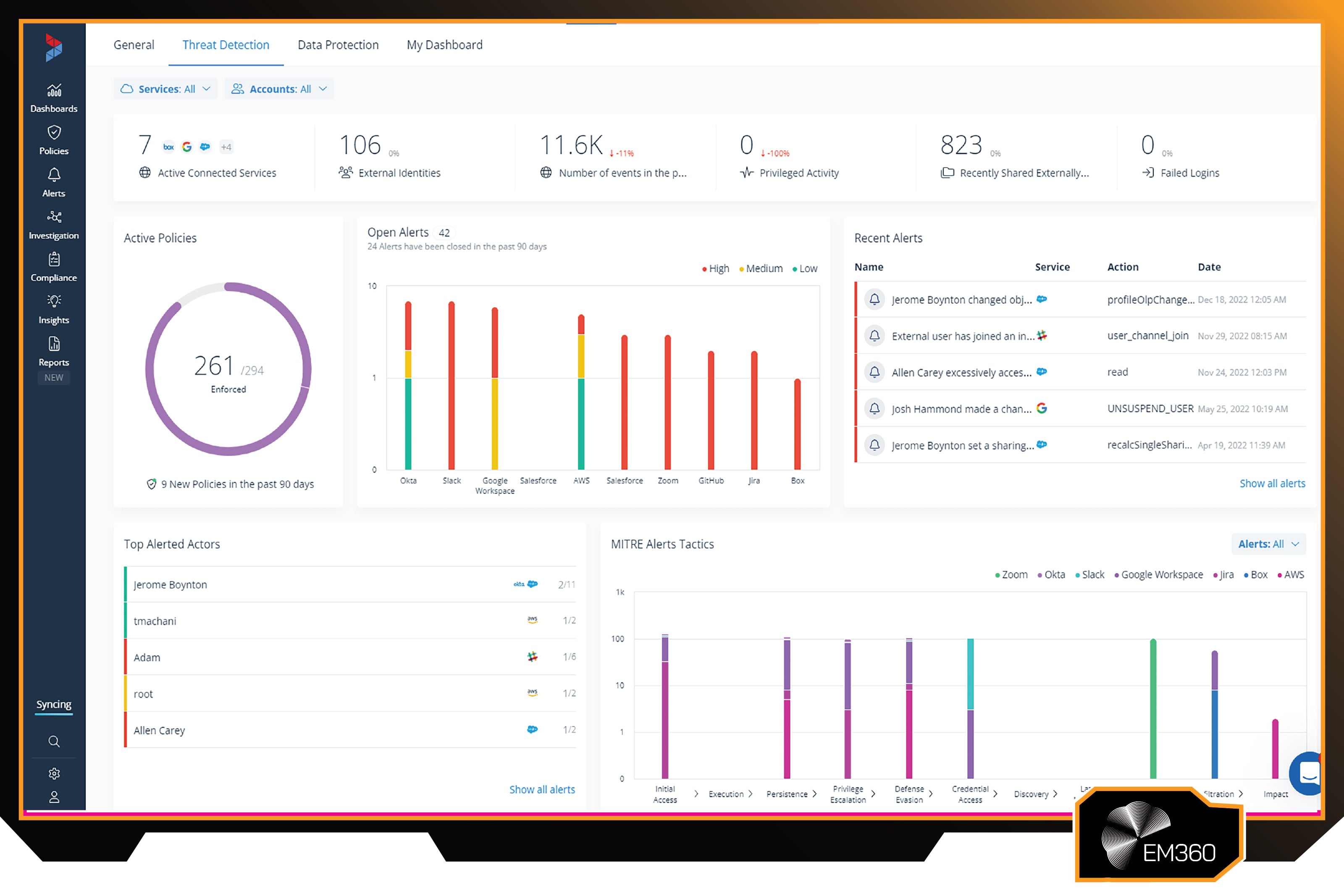
Varonis is a data security company focused on reducing risk in the places enterprises often struggle to control: unstructured data stores and cloud collaboration environments. The Varonis Data Security Platform has evolved around a consistent goal: helping organisations understand who can access sensitive data, who is actually accessing it, and where permissions have become too broad over time.
As enterprises expanded into Microsoft 365 and cloud repositories, Varonis extended its visibility and control model to match the realities of distributed access and growing insider risk.
Enterprise-ready features
Varonis continuously analyses data permissions, usage patterns, and content sensitivity across common enterprise environments such as file servers, NAS platforms, and Microsoft 365 storage and collaboration services. This allows it to identify where access is too open and reduce exposure by recommending or automating permission changes that enforce least privilege.
By pairing permission insight with an understanding of what data is sensitive, the platform helps security teams focus on the highest-risk areas first, rather than treating access issues as a generic clean-up task.
The platform also uses behavioural analytics to detect unusual access patterns that may indicate insider misuse, compromised accounts, or ransomware-style activity. Instead of relying on single events, it builds context over time, then alerts when behaviour shifts into risky territory, and it can support automated response actions to contain issues quickly.
This approach makes Varonis particularly useful for organisations that want to shrink internal exposure while improving their ability to detect and respond to suspicious data access before it turns into a breach.
Pros
- Excels at finding and fixing internal access control issues, ensuring sensitive data isn’t broadly exposed internally.
- Powerful anomaly detection for file access can catch insider threats and malware (like ransomware) early in the attack cycle.
- Integrates content classification with activity monitoring, giving context to alerts and enabling risk-based prioritisation.
- Provides actionable intelligence and automation (like removing global access groups or locking accounts) to reduce the manual workload on security teams.
- Increasingly cloud-savvy, extending its proven data protection model to popular cloud services and SaaS platforms.
Cons
- Focuses on internal data stores. It’s not a traditional DLP for monitoring or blocking data sent outside (though it might notice unusual bulk file reads before exfiltration).
- Generates a lot of telemetry; if not tuned, initial deployments can produce many alerts that require refining (though this is common with security analytics tools).
- Licensing can be modular and thus potentially costly if you need to cover many different platforms (files, email, cloud apps, etc., each might be a separate module).
Best for
Varonis is best suited to enterprises with large volumes of unstructured data that need stronger visibility and control. It’s a strong fit for organisations worried about excessive internal access, unclear permissions, or limited oversight into who is touching sensitive files. For teams under pressure to audit data access or reduce ransomware risk, Varonis provides focused monitoring and early detection that strengthens overall data security.
Common Pitfalls When Deploying Data Protection Tools
Even the best enterprise data protection platform can fail if it’s deployed without intent. The tools are only one part of the equation. Strategy, tuning, and ownership determine whether they reduce risk or simply add noise. For leaders, the real question isn’t whether you’ve bought the right technology. It’s whether you’re using it in a way that actually changes behaviour and lowers exposure.
Treating data protection as a compliance checkbox
One of the most common mistakes is treating data protection as something you install to satisfy an audit. A DLP system goes live, a few baseline policies are turned on, and the programme is considered complete. But when policies are copied straight from regulation text without aligning them to real workflows, the result is predictable. Either everything triggers an alert, or nothing meaningful does.

Data protection isn’t a one-off project. It’s an operating model. The difference shows in the objectives. If the goal is simply “pass the audit,” the tool becomes a reporting engine. If the goal is to reduce specific risks, protect defined data assets, or enable safer digital initiatives, the tool becomes a control layer. The shift is subtle, but it’s what turns compliance spend into strategic value.
Over-alerting without context or automation
Alert fatigue isn’t theoretical. Turn on every default DLP rule in a large enterprise and you can generate hundreds of alerts a day. When every minor policy breach looks urgent, the urgent ones disappear into the noise.
Modern data protection platforms include context signals such as user risk scoring, behavioural patterns, and data value tagging for a reason. They allow teams to prioritise what actually matters. Automation matters too. If routine issues can be handled through automatic quarantine, blocking, or guided user prompts, analysts can focus on higher-risk events. Fewer, richer alerts lead to faster and more confident decisions.
Ignoring ownership and accountability
Data protection doesn’t live in IT alone. When tools repeatedly flag the same exposed folders or misclassified documents and no one in the business owns the fix, nothing changes. Technology can surface risk, but it can’t assign responsibility.
Strong programmes define data owners and make expectations clear. Department leaders understand what data they’re accountable for. Employees know how to classify information and why certain controls exist. When that culture is in place, tools stop feeling restrictive and start acting as support. A prompt before sharing sensitive data becomes guidance, not friction. That’s when data protection moves from enforcement to enablement.
How to Choose the Right Data Protection Tool for Your Organisation
Choosing a data protection platform isn’t about picking the most well-known name. It’s about fit. The right decision depends on where your sensitive data lives, how mature your security operations are, and what your organisation will look like in three years, not just today. The tools in this list solve different problems. The value comes from matching them to yours.
Aligning tools to data types and environments
Start with your data reality. Is most of your risk sitting in structured databases, sprawling file shares, SaaS collaboration platforms, or a mix of all three? A database-heavy environment may need something built for structured monitoring and granular query control, while an organisation drowning in shared drives will need deep visibility into unstructured files and permissions.
Environment matters just as much. Cloud-native businesses often benefit from platforms designed to integrate directly with SaaS and identity systems, while enterprises with legacy infrastructure may still need on-prem or hybrid coverage. The goal is simple: protection should follow the data wherever it lives. Sometimes that means investing in a new platform. Other times, it means fully using capabilities you already license but haven’t operationalised.
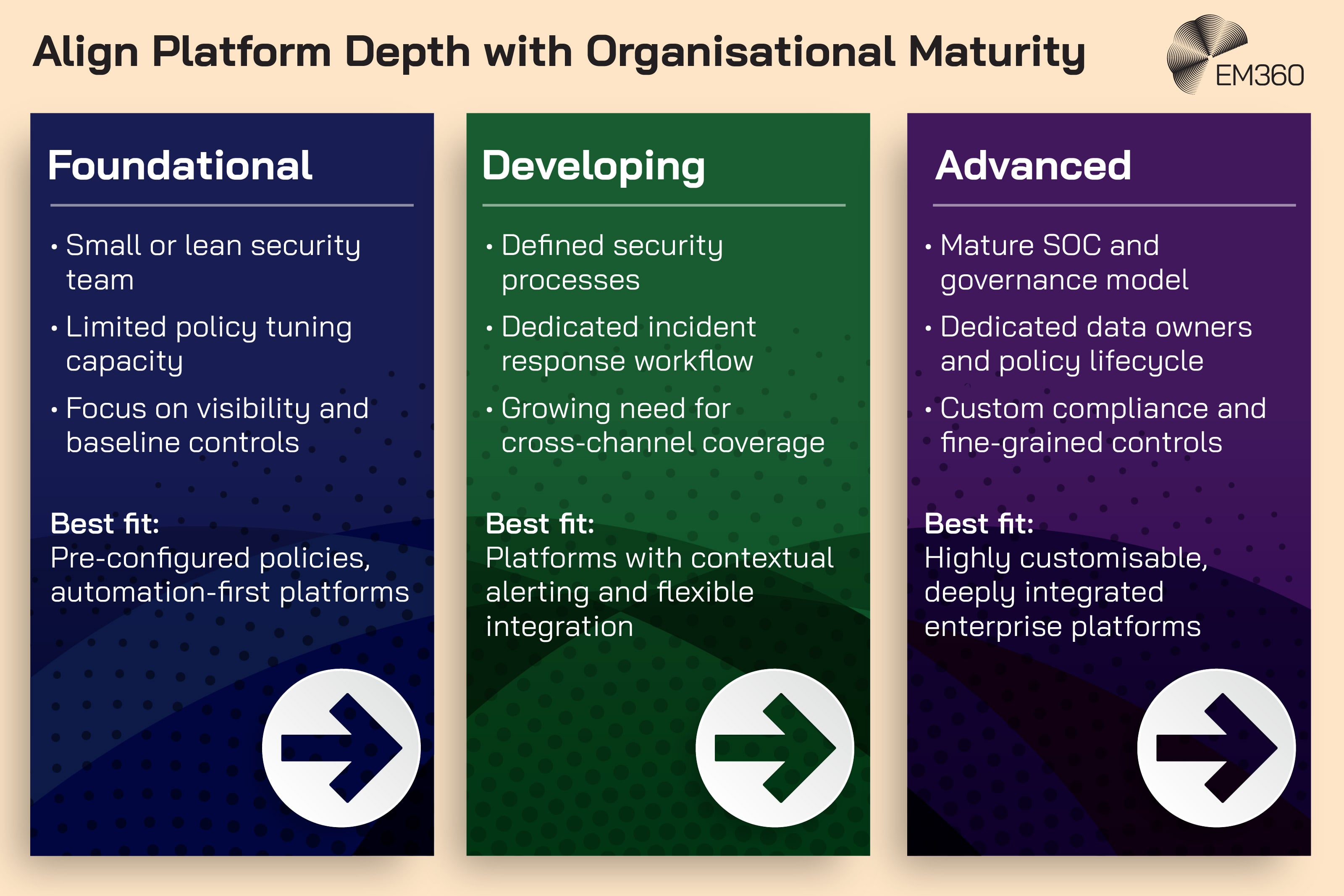
Matching platform depth to organisational maturity
Not every enterprise is at the same maturity level. A sophisticated DLP platform with endless tuning options can overwhelm a lean team. At the same time, a lightweight tool may frustrate a mature security operations centre that expects detailed analytics and tight policy control.
Be realistic about your internal capacity. Do you have people who can continuously tune policies, review incidents, and refine workflows? If not, look for platforms with strong automation, pre-built policy templates, or managed service options. A well-used mid-tier platform will always outperform an advanced system that sits partially configured and rarely reviewed.
Building for the next three years, not the last three
Data protection decisions have a long shelf life. The environment you’re securing today will evolve. Cloud adoption will deepen. AI tools will multiply. Regulatory expectations will tighten. The question isn’t whether change is coming. It’s whether your chosen platform can adapt without a full replacement cycle.
Look for solutions that are cloud-ready, update frequently, and integrate through APIs so they can plug into new workflows. At the same time, don’t get distracted by future features if the fundamentals aren’t strong. Discovery, classification, and enforcement still matter most. The best choice balances immediate risk reduction with the flexibility to grow as your data landscape becomes more complex.
Final Thoughts: Data Protection Is the Control Plane for Modern Enterprises
In 2026, enterprise data protection is more than just a set of defensive tools. It’s the connective tissue that allows a business to operate with confidence in a digital world. With data spread across countless devices, cloud services, and AI systems, a well-implemented data protection program acts as a control plane, giving organisations unified visibility and command over their most valuable asset (information) wherever it goes.
This control plane doesn’t stifle innovation; it enables it. When you know your data is classified, monitored, and guarded, you can embrace new technologies like AI assistants or cloud analytics without walking into the unknown.
For enterprise IT leaders and decision-makers, the journey doesn’t end with picking the right tools. It’s about fostering an organisational mindset that values data and proactively shields it. As you plan and refine your strategy, remember that you’re not alone. EM360Tech is here as a source of practical insight to keep you informed with best practices and emerging trends in enterprise technology.




Comments ( 0 )