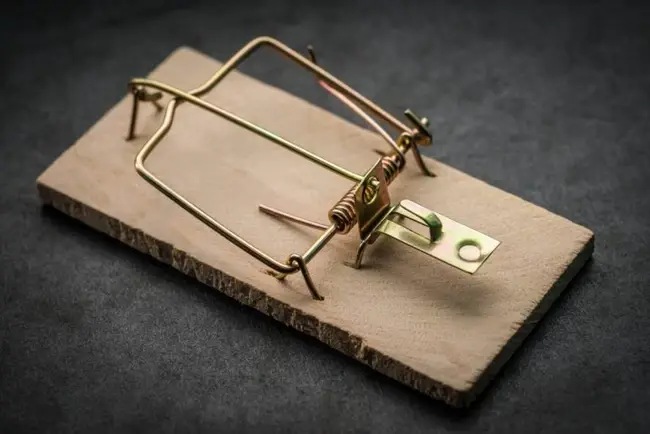
"Attackers only have to succeed once. The defenders have to succeed all the time." The odds feel as though they are ever in the favour of cyber attackers. Malicious actors are suffocating businesses, not just because of their growth in numbers, but the increasing complexity and sophistication of their attacks too. In other words, malicious actors always have the upper hand. As a result, attacks are no longer a question of 'if', but a question of 'when', forcing businesses to get it right 100% of the time. That's a lot of plates to spin. However, just because the power always seems to be with the attackers, it doesn't mean we have to accept it. Instead, we need to be thinking outside of the box to outsmart attackers with something different. One way of doing so is to fight fire with fire. For decades, cyber attackers have swindled businesses and individuals alike through Trojans and general trickery. Now, it's possible to give malicious actors a taste of their own medicine by playing them at their own game.
Do it better with deception
Deception technology is a cybersecurity measure that is highly appropriate for today's threat landscape. This unique approach to cybersecurity uses deceit to stack the odds in your favour. It works by laying a number of decoys to swindle attackers. These decoys act like breadcrumbs, often posing as legitimate assets that attackers may wish to sink their teeth into. Thus, when malicious actors reach your decoy, they may think they've hit jackpot – but you know they haven't. Deception technology gives you early insight into an attack by alerting you immediately of a malicious presence (often through scanning tools). This allows you to safely observe as they roam around your network. Of course, this is in stark contrast to the usual attack response, which is to shut everything down with haste. Instead, deception technology allows organisations to watch an attack that is essentially harmless to gain intelligence into how attackers are penetrating the network and how they move while they're there. This style of cybersecurity also eliminates the chance of false positives, wasting less critical time of your defence teams. Instead, deception technology promises only real alerts that require immediate attention.
It's time to get illusive
The Illusive Networks offering is a good example of how organisations can benefit from deception technology. With this solution, you can turn your endpoints into a cyber trap. In particular, the Illusive Attack Detection System blankets the entire network with fake information. This then forces the attacker to reveal themselves. In other words: ambush time. Attackers are lured in through Illusive's featherweight deceptions, planted at every endpoint. These deceptions mimic the assets your attacker seeks to get their hands on, including your data or credentials. In the meantime, you will quickly be alerted to any rogue activity and will be able to assess how far the attacker is from your legitimate critical business assets. Thus, you can take the immediate appropriate action to stop them in their tracks. Illusive's offering promises to put defenders in the driving seat. Given the current climate, it's not only the best seat to be, but the only.
Don't miss our Top 10 Identity Verification Software Solutions.




Comments ( 0 )