We send a lot of information over the internet, including sensitive and personal messages. As these messages travel across cyberspace, chances are that they can get intercepted by threat actors.
This is why it is more important for individuals and businesses to take an extra step to protect their information sent across the web. Imagine your messages being converted into a secret code, and sent only to the people you want it to be read by and have the key to decipher it.
That technology exists – it’s called encryption. It is a way to secure communications by scrambling your data so that it becomes illegible if they are intercepted.

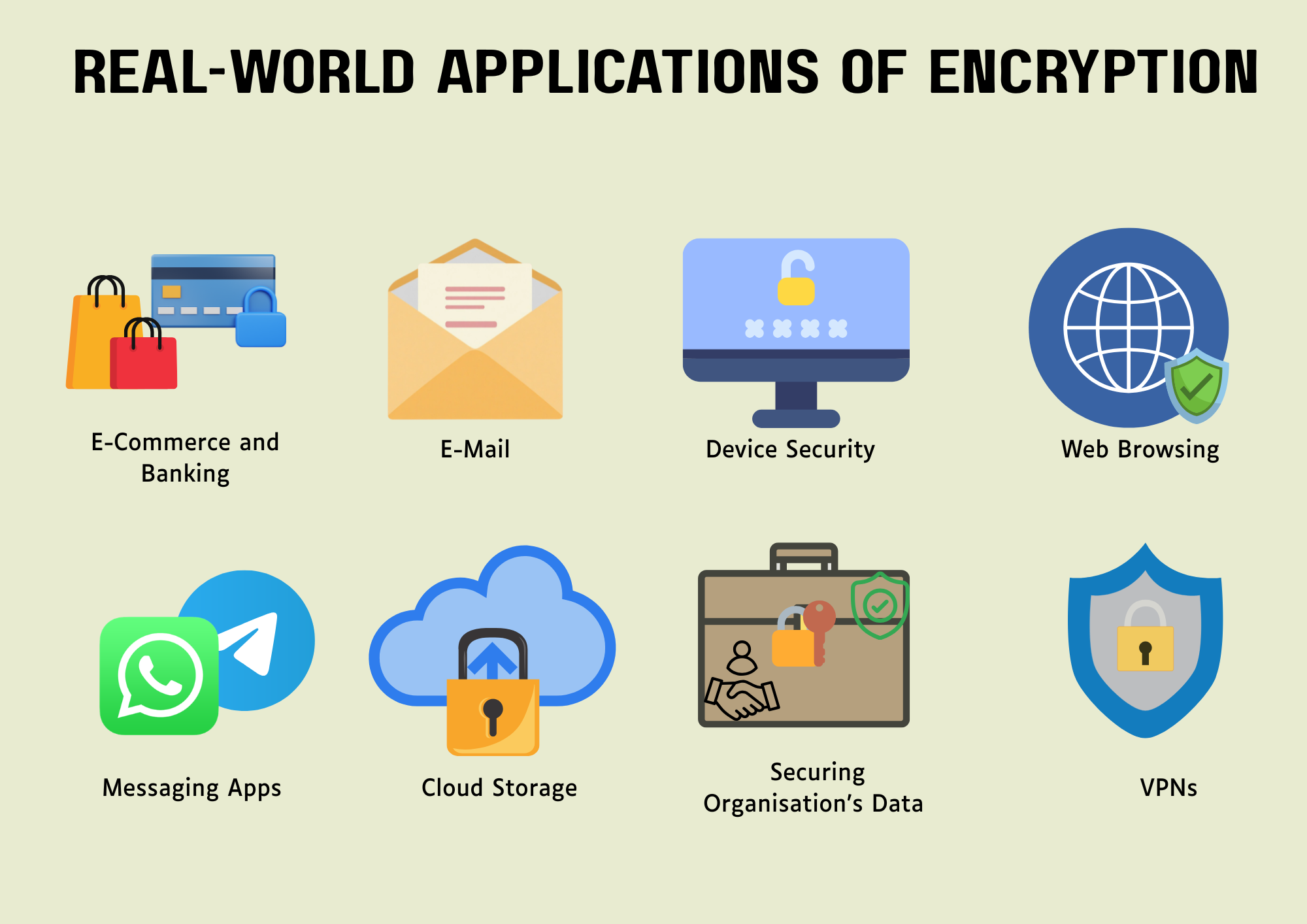
Several platforms like emails, online shopping and banking websites already encrypt information sent between users’ devices and the service providers. But with tools like public key encryption, individual users and organisations can encrypt their messages on their own to add an extra layer of protection to their information sent online.
What is Encryption?
Encryption is a process that uses a secret key or algorithm to encode and decode sensitive information. This makes sure that only those with access to the key can read it.
There are different types of encryption methods. But they can be broadly grouped into two categories: asymmetric and symmetric encryption.
Asymmetric Encryption
Also known as public key cryptography, this type of encryption uses two separate keys: one private and the other public. The public key is used for encryption, and the corresponding private key for the decryption process.
The public key is openly available or shared with authorised recipients without any worry of compromising security. But the private key is kept secret and never shared. Only the private key owner can decrypt the message.
Although this methodology is slower and more expensive, it is a much stronger option and hence, commonly used to ensure the security of the data transmitted across the web.
This encryption is largely applied for email security, web security, in messaging apps like WhatsApp, Signal and Telegram and e-commerce transactions.

When AI Becomes Your Companion
Explores AI companions as tools against loneliness, and what constant, unsolicited engagement means for human relationships at scale.
Symmetric Encryption
Unlike asymmetric encryption, this methodology only uses a single key for both encryption and decryption. A private key must be shared between both parties before they can decrypt it.
This sharing makes it less secure than asymmetric encryption, because if an unauthorised party gets access to the key, they will be able to decipher the data.
Since this private key cryptography uses one shared key, the process is faster and less expensive and hence effective in encrypting data in bulk.
Symmetric encryption is widely used for data storage, device and network security.
Why Encryption is Important
A robust encryption strategy is essential to safeguard data, especially for businesses, where data loss and breach can put them at huge financial risk and reputational damage.
Data encryption protects people’s privacy and keeps the communication between client apps and servers secure and ciphered (made into an unreadable format, like codes) so that cyber attackers won’t be able to read or use them to their advantage.
Encryption performs the following important functions:
Engineering GDPR-First Systems
Blueprint for building data minimisation, strong defaults and E2E safeguards into apps and data flows to operationalise Article 25 at scale.
Protecting Sensitive Data
Encrypting data protects confidential information by creating an impenetrable shield against hackers and unauthorised users. It converts the messages into an unreadable format so that even if they are intercepted, the content cannot be accessed without the key for decryption.
Ensuring Data Integrity
Encryption, paired with other cybersecurity methods like hash functions, ensures that the original data remains unaltered during transmission or storage. This is to thwart attackers from committing fraud and extortion by manipulating the contents.
Helps Meet Compliance Requirements
Many frameworks and security regulations require strong encryption for securing sensitive data, maintaining privacy and preventing unauthorised access.
Verifying the Sender
Encryption helps in verifying the origins of the data and its authenticity. It prevents the sender from denying sending a message and ensures that the contents have not been tampered with.
Encryption confirms the sender’s identity because the message is signed using the sender’s private key. The principle behind this is called non-repudiation, which enhances the security in digital communications and ensures reliability.

AI Chatbots and Data Exposure
Examines how everyday prompts, corporate secrets and model training pipelines create new attack surfaces for adversaries.
How Encryption Works
The whole process works through encryption keys – they act as the gatekeepers by safeguarding data and controlling who can decode the encrypted message.
These keys use complex mathematical formulas and algorithms to scramble the messages or encrypt them as codes that are illegible, so that they are protected from exploitation by the wrong hands even if intercepted.
In asymmetric encryption, two keys are generated: a public key and a private key. The public key is shared openly while the private key is kept secret. Both are used to encrypt and decrypt messages. For example:
A wants to send a confidential message to B. To do so, A would use B’s public key to encrypt it and use A’s own private key to sign the message. This step confirms the sender, A’s identity.
B would decrypt the same message with the associated private key that B is in possession of. B will not share this private key with anyone, as it is like a password that should be kept secret so that only B can read the sensitive information.
However, in symmetric encryption, only one private key is used to encrypt and decipher the messages. So, A and B share the same key to convert the plaintext (original message) to ciphertext (coded or encrypted message) and then decode or decrypt the data to a readable format.
Encryption can be applied to data while “at rest” and “in transit”. When it is stored in a database or a server, that is, when data is “at rest”, encryption is essential as it is constantly at risk of breaches. Encrypting data in transit secures it as it is transmitted across the internet.
When Chat Apps Become Crime
Criminal networks are shifting operations into encrypted messaging, challenging law enforcement models and cross-border governance.

Encryption also relies on encryption algorithms. They are mathematical formulas used in the conversion of plaintext to ciphertext. Blowfish, Advanced Encryption Standard (AES), Rivest Cipher 4 (RC4), RC5, RC6, Data Encryption Standard (DES), and Twofish are some widely used encryption algorithms.
Using these algorithms along with the encryption keys makes the encryption process stronger for defending data against cyber-attacks and unauthorised access.
Challenges & Limitations
Key Management
If the keys are lost or not secure, attackers can easily gain access to the organisation’s data. With technology evolving every second, cyber-attacks are also taking new forms and becoming stronger than before. So, even though decrypting data is extremely difficult, attackers who are always looking for loopholes can exploit even the slightest vulnerability to gain access to the data.
Poor key management can compromise the whole security of the system to data breaches and unauthorised access.
Encryption alone is not enough
Encryption can complicate system performance. Encrypting large amounts of data and the complexity of encrypting across a large network, such as an entire organisation, can impact system performance.
Companies must regularly audit their encryption practices and update encryption protocols. They should implement access controls within the organisation and train employees on encryption.
Choosing sophisticated encryption methods over traditional ones, like quantum encryption, can significantly defend data against malicious attacks.
Takeaways
Using encryption methods to secure sensitive data is an important strategy to enhance an organisation’s cybersecurity. By converting original data into illegible and coded data, and ensuring that only the private key holder gets access to the authentic data, it protects sensitive data from being exposed.
Finance and banking, healthcare, e-commerce, and other sectors, and governments, use encryption to safeguard classified information stored in databases and transmitted across the web.
While encryption adds an extra layer of protection to your data, it is also equally important to combine it with other, even basic, cybersecurity practices like using strong passwords and enabling multi-factor authentication.
Companies must ensure regular audits are conducted, encryption protocols are updated, and employees are trained on the use of encryption and the importance of securing data.
Encryption and cybersecurity together can act as a powerful shield against malicious attacks by protecting the organisation’s digital assets, data integrity, confidentiality and securing their digital communications.







Comments ( 0 )