The Security Strategist is EM360Tech’s enterprise security podcast, built around the conversations enterprise leaders are already having as cybersecurity moves from the server room into the boardroom. Hosted by experienced security analysts and featuring technology experts from across the industry, the series looks at how organisations turn enterprise security strategy into systems that actually work in modern environments.
That shift matters because enterprise cybersecurity used to sit more neatly inside technical teams. It was still high stakes, still complicated, still business-critical. But it was easier to treat as a specialist responsibility. That isn’t really true anymore.
Security decisions now reach into almost every part of the organisation. They shape how people access systems, how applications connect, how data moves, and how new technologies are adopted. At the same time, the environment keeps shifting. Threats evolve quickly, attack surfaces expand, AI introduces both opportunity and risk, and regulations tighten.

Security leaders are expected to keep the organisation protected without slowing it down, which is where things usually get complicated. That’s why enterprise cybersecurity now lives as much in strategic decision-making as it does in technical controls. The hard part isn’t only knowing what a technology does.
It’s understanding what that decision changes everywhere else. The Security Strategist sits in that
What The Security Strategist Podcast Is All About
The Security Strategist is EM360Tech’s podcast series focused on the decisions that shape how security works in practice. The reality where security leaders need clearer thinking, better questions, and conversations that don’t fall apart the moment real-world complexity shows up. That distinction matters.
Plenty of cybersecurity content explains the latest threat, the latest tool, or the latest acronym. Useful sometimes, yes. But enterprise leaders usually need something a little more grounded than that.
They need to understand how security programmes are actually managed, how security models adapt to modern environments, and what happens when strategy meets operational reality.
That’s where this series is most useful.
The conversations don’t treat cybersecurity as one tidy category. They deal with it the way organisations experience it: as a mix of identity, access, applications, governance, infrastructure, policy, architecture, and constant compromise between what would be ideal and what is actually possible.
Some discussions lean more heavily into leadership decisions. Others focus on architectural implications or implementation pressure. The common thread is that they all stay connected to how enterprise security functions in the real world.
That also makes the series a natural fit within EM360Tech’s wider role. EM360Tech has built its reputation around helping enterprise technology audiences make more informed decisions. The Security Strategist extends that into cybersecurity by making complex issues clearer without flattening the difficult parts.
Security Strategy Through An Analyst Lens
The quality of a security conversation often depends on who’s steering it. Not because they need to dominate it, but because cybersecurity is full of ideas that sound simple until someone pushes on them properly.
That’s where the analysts matter.
The Security Strategist is guided by analysts and recognised security experts who bring independence, structure, and context into the discussion. Their role goes well beyond asking questions and keeping time. They challenge assumptions. They connect individual issues to broader enterprise risk.
They spot where a neat answer has skipped over a complicated reality. In other words, they do the work good analysts are supposed to do. That matters because enterprise cybersecurity is full of language that can become vague very quickly. Zero Trust is a good example.
It sounds clear enough on paper, but the moment you start applying it across a large organisation, questions pile up fast. How much friction is too much? What does trust actually look like in a distributed environment? Which controls improve security, and which ones just make work harder? A strong analyst doesn’t let those tensions stay buried.
Across the series, figures such as Alejandro Leal, Richard Stiennon, Chris Steffen, Brad LaPorte, and others help keep the conversations at that useful level. They bring strategic insight, market awareness, and the ability to connect technical questions to organisational consequences. That changes the quality of the discussion.
It also makes the podcast far more valuable to enterprise audiences who aren’t looking for a glossy summary. They’re looking for thinking they can actually use.
Security Leaders Sharing Their Practical Experience
If analysts bring perspective, guest experts bring friction. Useful friction, to be clear. The kind that appears when theory runs into implementation.
The Security Strategist regularly features guests from across the enterprise security ecosystem, including founders, chief executives, chief technology officers, field chief technology officers, and subject-matter specialists working in security-focused organisations.
These are people who spend their time dealing with the real constraints enterprises face: legacy infrastructure, fragmented visibility, complex access requirements, operational bottlenecks, governance pressure, and the awkward reality that stronger controls can create new problems elsewhere.
That practical experience gives the series real weight.
A discussion about identity security lands differently when it includes someone working directly in that space. The same goes for API security, internal access architecture, or changing trust assumptions in modern environments.
Guests can speak to how organisations are trying to solve these problems, where they get stuck, and what usually proves harder than expected. That makes the conversations more honest and much more useful. There’s also a strategic benefit for the organisations involved.
EM360Tech already operates as a thought leadership platform in enterprise technology, and the podcast gives security leaders a credible space to contribute to those conversations. When they do it well, they show how they think about the problem, how they understand the market, and where their expertise fits into the wider security landscape.
That kind of visibility builds trust far more effectively than a polished sales line ever could.
Inside The Security Conversations Driving The Series
The easiest way to understand what The Security Strategist does well is to look at the conversations themselves. The strongest episodes don’t just describe a problem. They show how enterprise security decisions ripple across architecture, operations, governance, and day-to-day work.
A strategic outlook on the cybersecurity landscape
The two-part Meeting of the Minds: State Of Cybersecurity in 2025 discussion gives a strong sense of the podcast’s overall range. Rather than narrowing in on one control area, it steps back and looks at the wider security landscape shaping enterprise decision-making.
The discussion moves across AI, regulation, platform strategy, integration challenges, and the broader pressures influencing cybersecurity leadership. That wider framing matters because enterprise security leaders rarely get to think in silos.
They’re making decisions inside an environment where market shifts, policy shifts, and technology shifts are all happening at once. A conversation like this helps put those moving parts into perspective. It also makes clear that the series isn’t only interested in technical detail.
It is equally interested in the strategic environment those technical decisions sit inside.
Identity security in an AI-driven world
Why AI Agents Demand a New Approach to Identity Security takes one of the most important control layers in modern enterprise security and shows how quickly it’s changing.

Identity has already become central to cybersecurity, especially as traditional perimeters have weakened and access patterns have become more distributed. AI agents add another layer of complexity. They introduce new forms of identity, new governance problems, and new questions around visibility and control.
The issue is no longer just whether the right employee has the right permissions. It’s also whether organisations can understand and manage non-human actors moving through their environments with growing levels of autonomy. That shifts identity from an administrative concern into something much more strategic.
It affects access, trust, governance, and the ability to scale securely.
Zero Trust and the growing pressure on CISOs
Why Are 94% of CISOs Worried About AI, and Is Zero Trust the Only Answer? sits in a slightly different but related space. It brings together AI-driven threats, identity fabric, and Zero Trust in a way that reflects the pressure many security leaders are already dealing with.
The conversation works because it captures a real leadership tension. AI is changing the threat landscape quickly, but security leaders still need approaches that hold up operationally. They can’t just chase every new concern with another isolated control. They need security models that make sense across the organisation.
That’s where the discussion becomes more than a question about AI risk. It becomes a question about architecture, trust, and how CISOs prioritise in an environment where the stakes keep rising and the edges keep moving.
Securing application ecosystems in the age of autonomous systems
What Happens to API Security When AI Agents Go Autonomous? brings the conversation into application ecosystems and API security, which are both easy to underestimate until something breaks.
APIs sit underneath a huge amount of modern enterprise activity. They connect systems, enable integrations, support workflows, and increasingly shape how applications and AI-driven services interact. Once autonomous agents begin operating across those environments, the security problem changes.
Visibility becomes more important. Governance becomes more important. So does a clear view of which systems are exposed, how they’re being used, and what kinds of control are actually in place. That makes the episode especially valuable because it shows how AI doesn’t only introduce abstract future risk.
It changes how existing parts of the enterprise environment need to be secured right now.
Rethinking internal security models for modern infrastructure
Is Traditional Client-Based Access Obsolete? Rethinking Internal Security tackles another question many organisations are now forced to confront: what assumptions about internal access no longer hold?
Traditional access models were built for more contained, more predictable environments. Modern infrastructure rarely behaves that way. Organisations now deal with different devices, different trust conditions, different user contexts, and different expectations around access speed.
That makes older models harder to rely on, especially if they introduce friction without delivering the right level of control. What makes this conversation useful is that it doesn’t stay at the level of technology preference.
It gets closer to the real issue, which is how organisations rethink trust inside modern infrastructure without creating unnecessary barriers for the people trying to work.
Security Leadership Is About Managing Trade-Offs
Once you look across these conversations together, a pattern becomes hard to miss. Enterprise cybersecurity isn’t really a collection of isolated technical choices anymore. It’s an ongoing negotiation between competing needs.
Security leaders are balancing protection against usability. Governance against speed. Visibility against complexity. Access against control. New capability against new exposure. None of those tensions are especially new on their own. What’s changed is how interconnected they’ve become.
Identity architecture affects how safely people and systems can interact. API security affects how applications communicate and how AI agents behave inside those environments. Internal access models shape user experience, trust assumptions, and security posture at the same time.
Broader strategic discussions then place all of that inside a larger context of regulation, architectural change, and evolving cyber risk. That’s why these episodes tend to move quickly beyond any single tool or control category.
They keep landing on the same underlying reality: security strategy succeeds when organisations can protect what matters without making the organisation impossible to run. That’s a much harder challenge than simply adding more controls. It’s also the one enterprise leaders are actually dealing with.
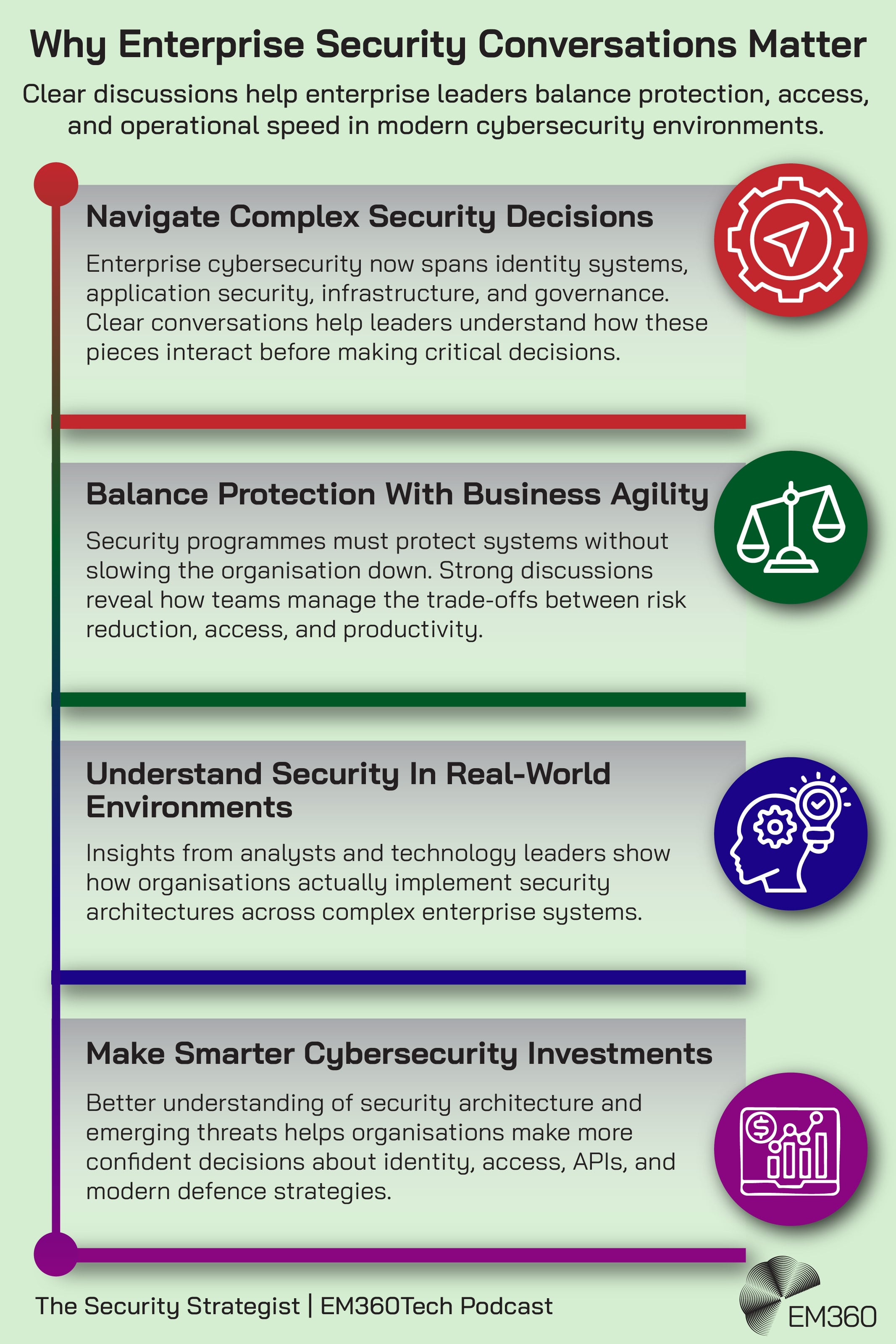
Why These Conversations Matter For Enterprise Leaders
For enterprise leaders, the value of a series like this and the ones happening on our other podcast series sits in the quality of the thinking it supports. The conversations help organisations prepare security strategies for evolving cyber threats without treating every new development like a reason to start from scratch.
They help leaders think more clearly about identity security in AI-driven environments, which is quickly becoming one of the most important pressure points in modern cybersecurity. They also make it easier to understand what Zero Trust and modern access controls look like once they leave the slide deck and meet real infrastructure.
That practical value carries across the wider themes as well. Enterprise teams can use these discussions to think through how APIs and application ecosystems should be secured as environments become more connected and more automated.
They can also use them to question whether older internal access models still fit the way their organisations actually operate. That is what practical thought leadership should do. It should help people make better decisions, not simply sound informed from a distance. And this same thinking guides our other podcast series as well.
Final Thoughts: Security Strategy Works When Protection And Operations Move Together
Enterprise cybersecurity has become too broad, too connected, and too consequential to be treated as a purely technical issue. The real challenge now is not only knowing which risks exist. It’s knowing how security choices shape access, governance, architecture, productivity, and the organisation’s ability to keep moving.
That’s what makes the conversations in The Security Strategist valuable. They don’t reduce cybersecurity to tools or headlines. They deal with it as enterprise leaders experience it, which is as a series of decisions that carry technical, operational, and strategic consequences all at once.
When analysts, practitioners, and security specialists work through those decisions together, the picture gets clearer. The trade-offs become easier to see. So do the assumptions that need challenging.
Readers who want to stay close to how enterprise cybersecurity thinking is evolving can follow the ongoing conversations in The Security Strategist series on EM360Tech.



