Hadrian
1
Followers
About
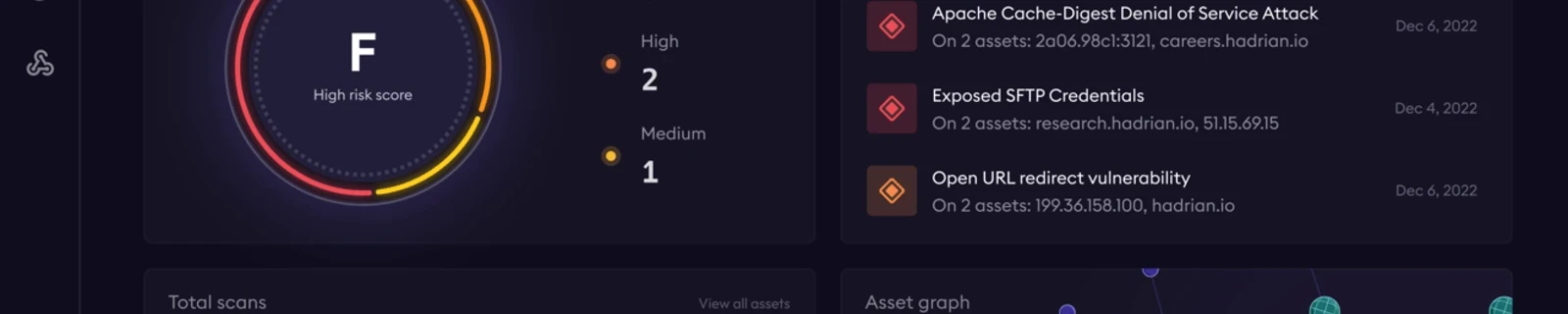
Hadrian is a leading provider of External Attack Surface Management (EASM), Continuous Automated Red Teaming (CART), and Continuous Threat Exposure Management (CTEM) solutions. Our platform catalogs known and unknown assets wherever they are, investigates vulnerabilities by identifying exploits like a threat actor, and prioritizes risks for fast remediation based on your unique environment.
Areas of expertise
Security