In the digital age, securing sensitive business information has never been more critical. Microsoft 365 has become the backbone of operations for organisations worldwide, and with that centrality comes an expanding attack surface that many security teams are only beginning to fully understand.
In a recent episode of the Security Strategist podcast, host Richard Stiennon sat down with Rob Edmondson, Senior Director of Product Marketing at CoreView, to unpack the practical realities of Microsoft 365 security. The conversation covered configuration drift, excessive privilege, tenant hardening, and the emerging security challenges posed by AI agents offering actionable guidance for security professionals at every level.
Microsoft 365 Environment
Microsoft 365 has changed significantly from a simple productivity platform into a comprehensive security concern in its own right. As Edmondson points out, the transition from Office 365 to Microsoft 365 marked a pivotal shift in how organisations utilise these tools. What began as a suite of familiar applications, such as Word, Excel, and Outlook, has grown into an interconnected ecosystem of over 60 apps and services, from Teams and SharePoint to Power Automate, Defender, and Purview. That expansion has delivered enormous productivity gains, but it has also multiplied the potential vectors for security vulnerabilities exponentially. Every additional service is a new configuration surface, a new set of permissions to govern, and a new integration that must be secured. Understanding this evolution is the essential starting point for any organisation serious about Microsoft 365 security.
Configuration Drift and Why It Puts Microsoft at Risk
Configuration drift is one of the most pervasive and underappreciated threats in Microsoft 365 environments. It refers to the gradual, often unnoticed divergence of system configurations from their original, secure baseline, which is a slow accumulation of small changes that individually seem harmless but collectively create significant vulnerabilities.
Edmondson highlighted that most organisations lack adequate visibility into how their Microsoft 365 tenant is actually configured at any given moment. Many still rely on manual methods like spreadsheets, periodic snapshots, and ad hoc reviews to track configuration state. This approach is fundamentally inadequate in environments where settings can change daily, sometimes through automated processes or third-party integrations that bypass normal change management controls.
The consequences of undetected configuration drift can be severe. Breaches have been traced directly to unauthorised or unintended configuration changes, a permissions setting quietly altered, an authentication policy weakened, or a data loss prevention rule inadvertently disabled.
When M365 Becomes the Perimeter
Boards are shifting from email-only thinking to treating Microsoft 365 as critical security infrastructure with tenant-wide blast radius.
Microsoft 365 Security Posture
Excessive privilege is consistently ranked among the leading contributors to security incidents in cloud environments, and Microsoft 365 is no exception. When users, service accounts, and applications hold more permissions than their role requires, the potential blast radius of any compromise — whether through phishing, credential theft, or insider threat — expands dramatically. Edmondson walked through the practical challenge: in large organisations, permissions accumulate over time. A user gets temporary admin access to complete a project, and that access is never revoked.
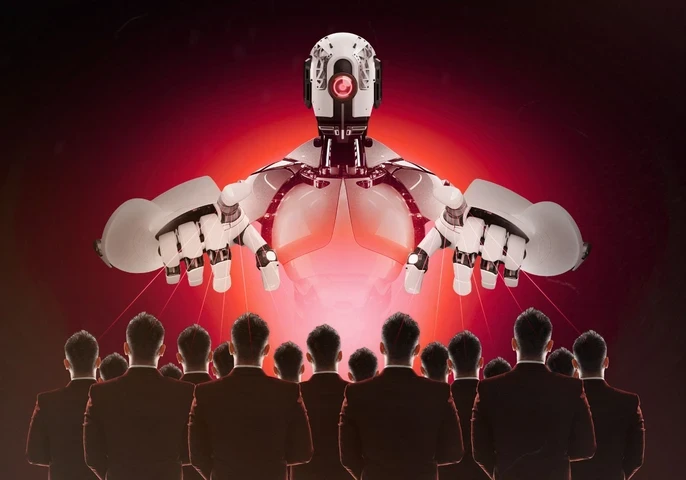
AI Agents in Microsoft 365
As organisations adopt AI-driven tools and agents within their Microsoft 365 environments, a new and largely uncharted security frontier is emerging. AI agents - automated systems capable of acting on behalf of users, reading emails, accessing files, and executing workflows — introduce permissions challenges that most security frameworks were not designed to handle.
Edmondson was candid about the challenge: many organisations deploying AI agents do not have clear visibility into what those agents can access, what data they are interacting with, or whether the permissions they hold are appropriate. In an environment where an AI agent might have access to the entire Microsoft 365 data estate of a user or a team, the consequences of a misconfigured or compromised agent are significant.
The same principles that govern human access with least privilege, continuous monitoring, and regular review must be extended to AI agents. This requires both the technical capability to enumerate agent permissions and the governance processes to enforce appropriate boundaries. Organisations that deploy AI capabilities without first establishing this control layer are trading short-term productivity gains for long-term security debt.

Inside M365 Tenant Resilience
How baselines, automated configuration snapshots, and drift monitoring turn Microsoft 365 from a fragile suite into an operational platform.
Microsoft 365 Security
In the fast-moving threat landscape, understanding and proactively strengthening your Microsoft 365 security posture is no longer optional; it is a business imperative. Configuration drift, excessive privilege, and AI agent governance are not edge cases; they are mainstream risks affecting organisations of every size and sector. The insights shared by Edmondson on the Security Strategist podcast provide a practical foundation for addressing each of these challenges with clarity and urgency.
By implementing continuous monitoring, enforcing least-privilege access, hardening your tenant configuration, and extending security governance to AI agents, organisations can significantly reduce their exposure and build a Microsoft 365 environment that is resilient by design. For further insights and tools to support your Microsoft 365 security journey, visit CoreView.
Takeaways
- Configuration drift and its impact on security.
- Excessive privileges and how to mitigate them.
- Tenant hardening best practices.
- Managing AI agents and permissions in Microsoft 365.
- Strategies for continuous security monitoring.









Comments ( 0 )